Bitwarden - Self-hosted password manager
-
I don't know enough about the internal workings of cloudron to give a definite answer, but from what I see I would guess your first install failed (because it could seemingly not fetch the right image) and now the app is in a failed state.
One way to get out of this is to try restore an earlier backup (but it also said
=> Backup - undefined) so its unclear if one exists, or remove the app and start anew. -
Thanks for the hint. In the control panel, I have the following error:
An error occurred during the operation: Docker Error: Unable to pull image. Please check the network or if the image needs authentication. statusCode: 404 -
Stupid me! My docker repository was set to private!
Once made public - at least for the time of updating - a simple click on "repair" in the Cloudron control panel was enough! -
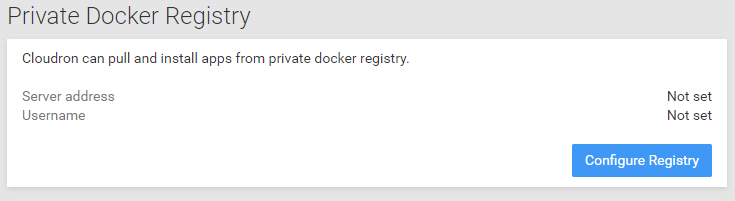
@necrevistonnezr then this here in the settings would probably be helpful for you:
-
For those using this. Does/will it support 2FA, and what kind? I'm mostly interested in Yubikey support. Thanks.
-
Happy New Year everybody!

Just learned how to deploy a custom app using Bitwarden as the test, but seeing as it should be delivered soon, figured I'd wait for the more official release. So on that note... is there any ETA yet for this app @girish or @nebulon by any chance? If it's going to be a month or two I may start with the custom app, but figured if it'd be just another week or two (or just less than a month), then I'll just wait it out.
Thanks again for all the work you guys do - including everyone else in this thread, as I was able to learn a lot from reviewing everything you all wrote!

-
Sorry for the delay, back to working on getting this published.
As a prelude, I have written to the upstream project to see if there is a chance of getting bitwarden (the .net project) working with a database other than MSSQL. As it stands, Cloudron cannot run the main project in a supported fashion.
Now for Bitwarden Rust, I built @iamthefij's project and it works great.
The current LDAP integration will essentially sync periodically and auto-invite users. I think this is awesome. However, Cloudron has a few limitations:
-
Apps are installed with 'all users' by default. This would mean all users on Cloudron will get invited/get email on installation. @iamthefij Maybe we can add a flag to not send email even if smtp is configured? My understanding is that this way LDAP users first have to 'create account' to get themselves an invite. Non-LDAP users won't get an invite. (https://github.com/dani-garcia/bitwarden_rs/wiki/Syncing-users-from-LDAP)
-
I guess we should disable users somewhere in https://github.com/ViViDboarder/bitwarden_rs_ldap/blob/master/src/main.rs#L107 when users go away from LDAP?
If 1 is not possible, I am also open to publishing the app without LDAP integrated directly. i.e we just include the binary and add docs to tell the user to run the command from the web terminal. That way they are aware email is going to be sent.
For 2, if you think that is outside the scope of an "invitation" system, then I think we should disable the ldap addon but include the bitwarden_ldap binary (this is just to be consistent with all our other apps wrt access control). We can add something in Cloudron to get credentials to the ldap server. That way, user can run the binary with the credentials directly.
-
-
@girish Do all users on the system automatically get invited? I didn't see that in my experience when I deployed the same app the other day, I had to manually invite myself through the /admin panel. I'm going to be a bit embarrassed if all my clients on the server got an email invite without me knowing

-
My understanding of the way it works is: Each Bitwarden user has a "master" password (also the login password). This password is set by a user when they setup their account (via an invitation email - this is the only way to finish account setup). There is no mechanism to create a user with a pre-setup password (like
changeme) on the server. This is because all the encryption/key generation happens on the clients. The clients get the master password, generate keys etc and just send it to the server.What this means is that Cloudron/LDAP password cannot be used as a login mechanism for Bitwarden. What the LDAP integration in the current Cloudron package does is to basically get the list of all users in Cloudron via LDAP and just sends them invitation emails (it does this periodically). This way each user can click on the invitation email, setup a master password and start using Bitwarden. Because Cloudron apps are installed with "all users" access restriction as the default, this would mean that the LDAP integration sends invitation email to all Cloudron users. In addition, if you change Cloudron/LDAP password or even delete the user in Cloudron, there is no effect in Bitwarden. This is quite different from how all other apps behave.
@d19dotca does that clarify?
-
Should be possible, like some other apps, to have the option of enabling automatic invites or forego it.
Technically, user management is local to the application. Invites is all that is really happening.
It should also be possible to silently invite users. This means that any user can sign up in the application directly as long as their email has been added to the invite list. May have to patch the core application for that, but certainly doable. If this sounds preferable, I can look into that.
As for disabling customers, it should also be possible. It was also planned, but just not implemented yet. Disabling does sound risky though as cutting off access to a password manager could be extremely disruptive.
-
@girish Yes I think that clarifies then. Thank you for explaining it. I thought from your earlier post you meant that all LDAP users registered on the Cloudron server would automatically be invited to use Bitwarden and I was worried there for a second. haha. My experience is what you explained most recently in that the invite needs to be manually done through the Bitwarden admin area.
-
@iamthefij said in Bitwarden - Self-hosted password manager:
This means that any user can sign up in the application directly as long as their email has been added to the invite list.
I think there was already an option to only allow signups from specific mail domains.
-
@fbartels yes. You can whitelist an entire domain. That will not allow whitelisting particular people on that domain though. So group or other constraints that we get with LDAP integration would not be supported.
The issue is that by default if sending mail is enabled Bitwarden will send an invite email with a particular invite code for any newly invited user: https://github.com/dani-garcia/bitwarden_rs/blob/88c56de97b48bb5b9b8af350d0d0e0d5f080ff0e/src/api/admin.rs#L163
An option to suppress this without disabling email entirely would allow whitelisting (and possibly revoking) users based on an LDAP query.
-
And done. Just pushed an update that allows disabling of SSO entirely and should fall back to the administrator manually inviting folks via the
/adminpage. I have not had a chance to test this though. -
@iamthefij That was quick. Can you put in a LICENSE file into the repo (preferably MIT like the other app packages), so I can get this pushed to unstable?
The optionalSso still has the issue that it will trick people into thinking it behaves like other LDAP apps. I think Cloudron needs to have some enhancement here to make the UX work reliably. For a start, I can push it out with LDAP syncing in place (i.e a person who wants to can run the tool manually from the terminal) but ldap addon removed.
-
@girish they won't be able to run it on a schedule, will they? If it was possible to schedule that, it would be great.
I just made some more updates to the Description to explain user management. I also updated the env variables set so they can be overridden by users (through the DB, CLI, or some new interface) to allow open signups, block invites, or whitelist a particular domain.
I can also add an MIT license file as long as @fbartels agrees, since I based it on his repo.
-
@iamthefij said in Bitwarden - Self-hosted password manager:
I can also add an MIT license file as long as @fbartels agrees, since I based it on his repo.
Almost forgot to reply here. I have added a license file to my repo now. So when you rebase yours you should get it as well.
