Can be closed, posted in Community Apps.
neoplex
Posts
-
IsoFlow on Cloudron - Isometric network and infrastructure diagrams (Community App) -
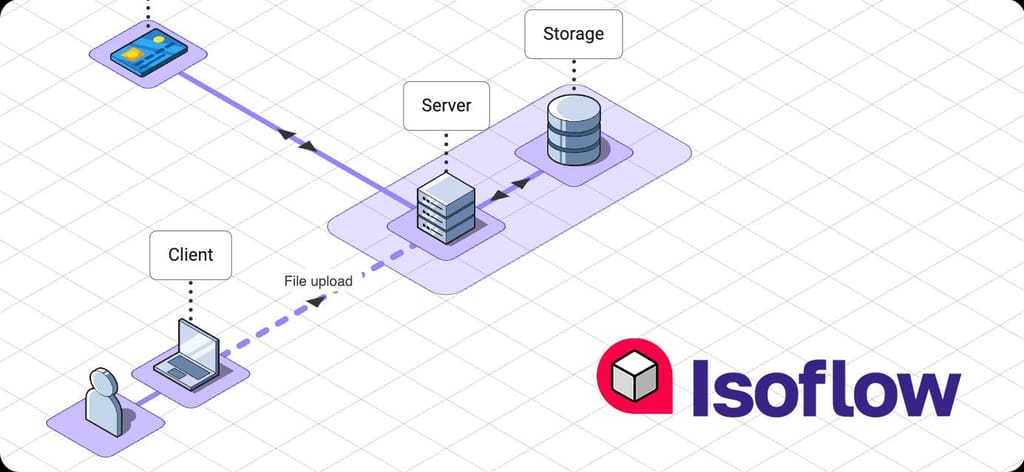
IsoFlow on Cloudron - Isometric network and infrastructure diagrams- Title: IsoFlow on Cloudron - Isometric network and infrastructure diagrams
- Main Page: https://github.com/pronetivity/cloudron-isoflow
- Git: https://github.com/pronetivity/cloudron-isoflow
- Licence: MIT
- Dockerfile: Yes
- Demo: N/A
- Summary: Browser-based isometric editor for network and infrastructure diagrams, packaged as a Cloudron community app.
- Notes: Maintained fork of the original IsoFlow Community Edition with Cloudron packaging, optional Cloudron SSO, JSON import/export, PNG export, and bundled icon packs for AWS, Azure, GCP, Kubernetes, and infrastructure diagrams.
-
Alternative to / Libhunt link: N/A
-
Screenshots:
-
"Failed to open stream: Permission denied" for cache/data@girish apologies, I jumped the gun on that last post. You were right.
I had a look at the box source code (
src/scheduler.js,src/docker.js) and the manifest command IS respected by the scheduler. Thephp artisan schedule:runon my instance came from a custom crontab entry carried over when we migrated from a standalone install to Cloudron over 2 years ago. That entry must have slipped through unnoticed, but it explains everything.After removing it, the scheduler container (now suffixed
-housekeepinginstead of-crontab.0) correctly runscron.sh:$ docker inspect --format '{{.Config.Cmd}}' 1af144bb-fbf4-434d-8edd-bb4b95c00ef5-housekeeping Cmd: [/bin/sh -c /app/pkg/cron.sh]Things are working correctly with
cron.sh+ gosu now
I should have caught this sooner. In my defense (barely), the Cron tab of the app doesn't mention that commands run as root. I eventually found it in the documentation at the bottom of the Cron page. A small note in the Cron tab itself would probably help others avoid the same mistake.
Cheers,
JD -
"Failed to open stream: Permission denied" for cache/dataWait one, I have a suspicion ...
-
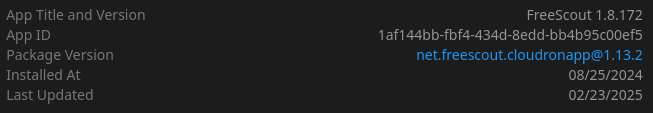
"Failed to open stream: Permission denied" for cache/data@girish you're right that
cron.shitself uses gosu. That part is fine. The issue isn't withcron.sh.The issue is the sidecar container that the scheduler addon creates. On the host:
$ docker ps --format '{{.Names}} {{.Command}}' | grep 1af144bb 1af144bb-fbf4-434d-8edd-bb4b95c00ef5-crontab.0 "/bin/sh -c 'php /ap…" 1af144bb-fbf4-434d-8edd-bb4b95c00ef5 "/app/pkg/start.sh"The sidecar doesn't run
/app/pkg/cron.sh. It runsphp artisan schedule:rundirectly:$ docker inspect --format 'Cmd: {{.Config.Cmd}} User: "{{.Config.User}}" Image: {{.Config.Image}}' 1af144bb-fbf4-434d-8edd-bb4b95c00ef5-crontab.0 Cmd: [/bin/sh -c php /app/code/artisan schedule:run >> /dev/null 2>&1] User: "" Image: cloudron/net.freescout.cloudronapp:202603171110280000No user is set (empty string), so it defaults to root. The gosu in
cron.shis never reached because the sidecar bypassescron.shentirely.This is easy to verify on any box with a freescout app running:
docker inspect --format '{{.Config.Cmd}}' <app-id>-crontab.0This is what creates the root-owned cache files under
storage/framework/cache/data/. -
"Failed to open stream: Permission denied" for cache/dataHey @girish, thanks for picking up the patch!
So, that one cleaned up the queue worker side of things (which was genuinely broken), but the root-owned cache files started appearing again. I've spent some more time on this and I FINALLY found the culprit ...
Turns out it's not anything inside the app container. It's the scheduler sidecar.
On the host:
$ docker ps --format '{{.Names}} {{.Command}}' | grep <app-id> <app-id>-crontab.0 "/bin/sh -c 'php /ap…" <app-id> "/app/pkg/start.sh"$ docker inspect --format '{{.Config.Cmd}}' <app-id>-crontab.0 [/bin/sh -c php /app/code/artisan schedule:run >> /dev/null 2>&1] $ docker inspect --format '{{.Config.User}}' <app-id>-crontab.0 (empty - runs as root)The sidecar runs
php artisan schedule:rundirectly as root every minute, creating scheduler mutex files and other cache entries understorage/framework/cache/data/owned byroot:root. When the app (running aswww-data) tries to write to those same directories - permission denied.Two things I noticed:
- The sidecar doesn't use the manifest's
"command": "/app/pkg/cron.sh"- which uses gosu to drop privileges - it hardcodesphp artisan schedule:runinstead - It runs without a user set, so it defaults to root
The fix from MR61 is still good to keep, but need to address the sidecar situation. For the freescout app specifically, I've now removed the
scheduleraddon and switched to running theschedule:runjob in the same container via a supervisor-managed process. That eliminates the sidecar container entirely.I've patched and tested the repo accordingly:
https://github.com/pronetivity/cloudron-freescout/commit/6771b826ee45cca6fc75d145f85d9d3da198daae
https://github.com/pronetivity/cloudron-freescout/blob/master/LARAVEL-CACHE-FIX.md
As for the scheduler sidecar - shouldn't it respect the manifest command (or run as the app user)? That would be a nicer fix at the platform level going forward.
Cheers,
JD - The sidecar doesn't use the manifest's
-
Wazuh - The Open Source Security PlatformIs there still interest in having Wazuh ported?
-
UniFi Network Server (was Unifi Cloud Controller)Has anyone worked on this in silence? If not, will port it

@girish This is a bit more complex as it needs to tie into mongodb and has a bunch of ports that have to be mapped. Generally, are you guys interested to move it to the appstore, once tested and stable? This isn't an open source app, so I am assuming, not? If that's the case, will just port it and set it up as a community app with a separate build pipe.
-
Healthchecks.io -- Cron job monitoringHas anyone worked on this in silence? If not, will port it

@girish This is as simple as smokeping in terms of implementation. Generally, are you guys interested to move it to the appstore, once tested and stable? Otherwise we'll package it as a community app and set up a build pipe.
-
"Failed to open stream: Permission denied" for cache/dataI am also going to leave this here:
I finally got around to putting together a fix:
https://github.com/pronetivity/cloudron-freescout/commit/27697c310fb373f1a972c7990f5c00dc3052ee54
A detailed analysis is available here:
https://github.com/pronetivity/cloudron-freescout/blob/master/LARAVEL-CACHE-FIX.md
Disclaimer: the commit also includes a few quality-of-life changes. The actual fix is limited to the caching adjustments.
Cheers,
JD -
SmokepingDone. Fully integrated.
-
SmokepingSuccessfully ported to a cloudron app. Will share link once I'm done testing.
-
"Failed to open stream: Permission denied" for cache/dataI've fixed this. Will send a patch via existing support email thread.
-
"Failed to open stream: Permission denied" for cache/dataYep!
-
"Failed to open stream: Permission denied" for cache/data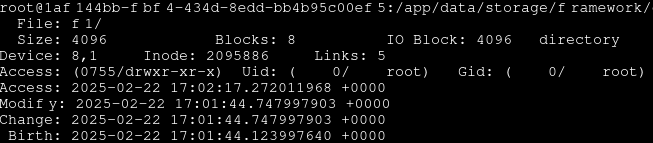
-
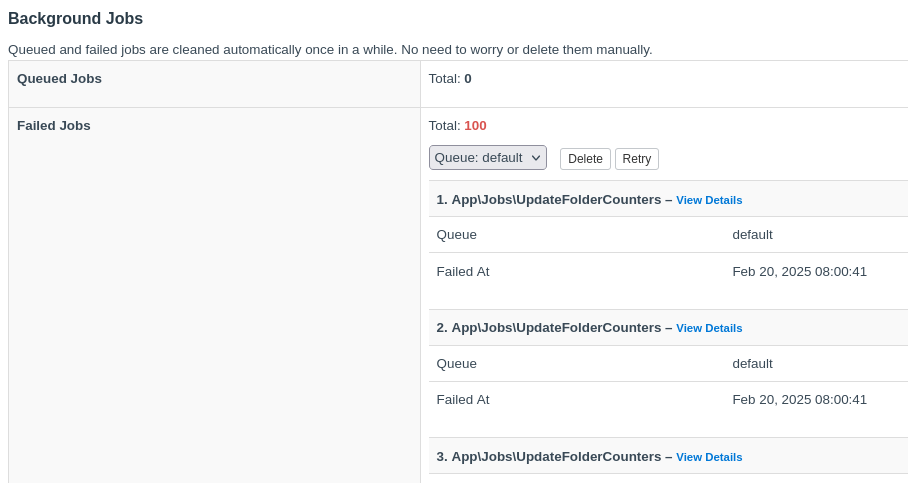
"Failed to open stream: Permission denied" for cache/dataIt's not the cron job. It's this job that's executed by the queue worker.
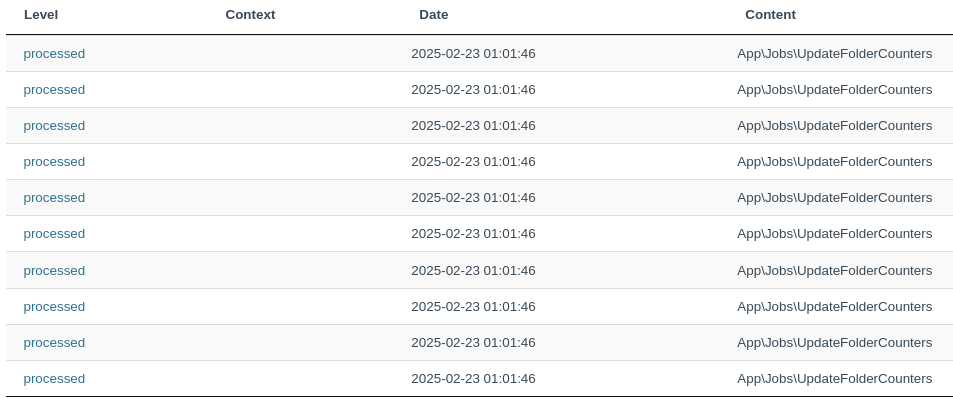
Although the PHP script that the queue worker is being executed with runs as
www-data.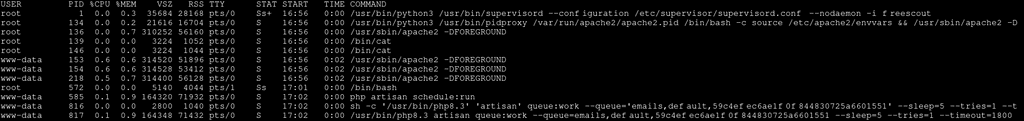
The timestamps match.
-
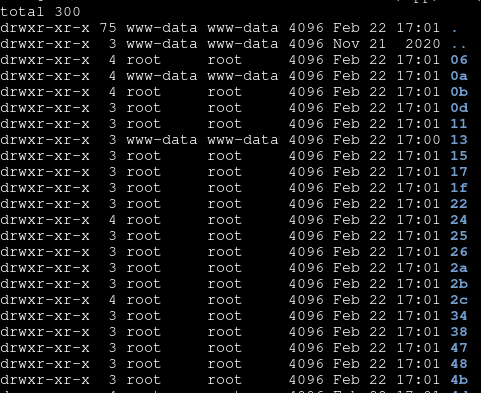
"Failed to open stream: Permission denied" for cache/dataIt appears that the directories owned by root are created either on the hour or at 45 minutes past the hour. And it seems to be related to those stalled
App\Jobs\UpdateFolderCountersjob. -
"Failed to open stream: Permission denied" for cache/dataAnyone else seeing this behavior?
Having trouble with files in the cache directory under
/app/data/storage/framework/cache/databeing created withroot/root, stalling background jobs and causing frequent disconnects in the frontend.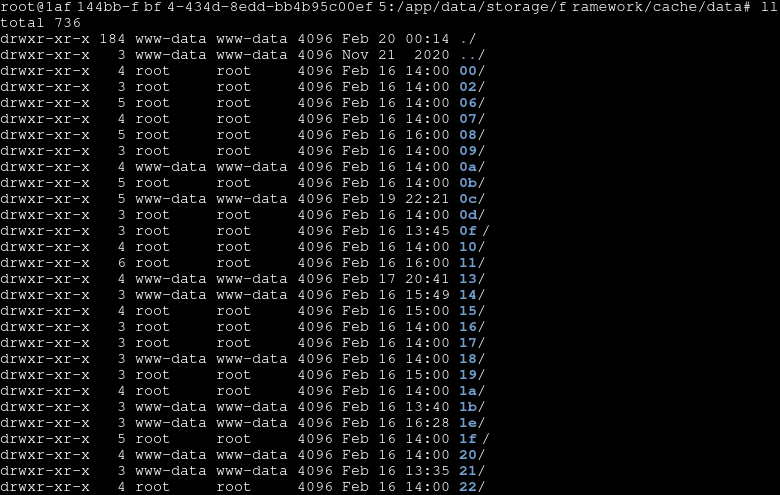
After changing the user/group for
cache/datadirectory recursively to www-data/www-data, things are working for a moment. Then the same thing happens again. I had a quick go around and couldn't find any obvious misalignment in the configuration or running processes. -
SmokepingThis is basically a static web frontend with a simple cron based backend. Hasn't seen any breaking updates in a decade and there are existing docker images for it. No one else interested?

I've looked through the app development guide and trying to find some time to build some images for cloudron.
