Cannot login anymore after switch to OIDC in latest update
-
With OpenID the apps backends have to be able to reach the OpenID provider, which on Cloudron is running on the dashboard domain. So any app with OpenID will fail if your system can't call the Cloudron APIs from within its app containers.
For a start, can you resolve the dashboard domain from the webterminal of an app?
host my.domain.comIf this is a system hosted behind a router (like a homesetup) make sure hairpinning is supported.
-
With OpenID the apps backends have to be able to reach the OpenID provider, which on Cloudron is running on the dashboard domain. So any app with OpenID will fail if your system can't call the Cloudron APIs from within its app containers.
For a start, can you resolve the dashboard domain from the webterminal of an app?
host my.domain.comIf this is a system hosted behind a router (like a homesetup) make sure hairpinning is supported.
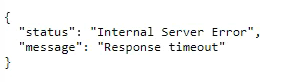
@nebulon It returns the public IP address. The system is behind a reverse proxy. The webinterface is reachable over the internet. Should I be able to open https://my.<your cloudron domain>/.well-known/openid-configuration from a browser?
I only get a server error.
-
Yes that should be publicly reachable. Can you check the server side logs at
/home/yellowtent/platformdata/logs/box.logabout any errors? -
If the local systems can resolve the public IP then this seems fine.
What kind of reverse proxy setup is this, maybe it interferes with the requests? Can you maybe disable that and expose the system directly just to see if it works as expected then? -
 N nebulon has marked this topic as solved on
N nebulon has marked this topic as solved on
-
Hello,
Now, I have the same problem at a customer. Cloudron and bookstack are not accessible from the internet. It is used only internal. I created a custom.conf for the unbound dns. But it is still not working. How do I have to configure the dns setting that OpenID Connect is working? We use a wildcard certificate.
-
Hello,
Now, I have the same problem at a customer. Cloudron and bookstack are not accessible from the internet. It is used only internal. I created a custom.conf for the unbound dns. But it is still not working. How do I have to configure the dns setting that OpenID Connect is working? We use a wildcard certificate.
@buesching said in Cannot login anymore after switch to OIDC in latest update:
But it is still not working
Can you tell us what is not working?
a) Can users reach the cloudron dashboard?
b) Is the app not able to reach the cloudron oidc api? Like maybe nothing appears after you click oidc button in browser?
c) Is that wildcard certificate self signed?If c) is the issue then fixing unbound won't help here. Most apps do not accept self signed certs for oidc. I recommend simply using a proper wildcard cert. You can either switch to one of the Cloudron supported DNS providers OR purchase a wildcard cert (it's only 45usd at https://www.garrisonhost.com/ssl-certificates/alphassl). In either case, you can keep your setup completely private as now.
-
@buesching said in Cannot login anymore after switch to OIDC in latest update:
But it is still not working
Can you tell us what is not working?
a) Can users reach the cloudron dashboard?
b) Is the app not able to reach the cloudron oidc api? Like maybe nothing appears after you click oidc button in browser?
c) Is that wildcard certificate self signed?If c) is the issue then fixing unbound won't help here. Most apps do not accept self signed certs for oidc. I recommend simply using a proper wildcard cert. You can either switch to one of the Cloudron supported DNS providers OR purchase a wildcard cert (it's only 45usd at https://www.garrisonhost.com/ssl-certificates/alphassl). In either case, you can keep your setup completely private as now.
@girish
a) yes
b) same error as in the 4th post. See above.
c) it is not self signed. Its from geotrust.We had the same problem in our environment. It was an misconfiguration of our reverse proxy (from the firewall).
In the environment of the customer the dashboards are note accessible from the internet. In that case the traffic does not run over the reverse proxy. The connection is established locally. -
If you are looking for some DNS solution to avoid the reverse proxy, you have to add something like this to unbound custom config:
server: local-zone: example.com typetransparent local-data: "my.example.com A 172.18.0.1"example.com is your dashboard domain . 172.18.0.1 is the internal oidc server for the app can reach.
-
@buesching Ah, all right. So, your issue looks like bookstack cannot contact cloudron dashboard because of the reverseproxy not looping back http requests. Is this sorted out now? Or are you still looking for assistance?
-
If you are looking for some DNS solution to avoid the reverse proxy, you have to add something like this to unbound custom config:
server: local-zone: example.com typetransparent local-data: "my.example.com A 172.18.0.1"example.com is your dashboard domain . 172.18.0.1 is the internal oidc server for the app can reach.
-
@girish
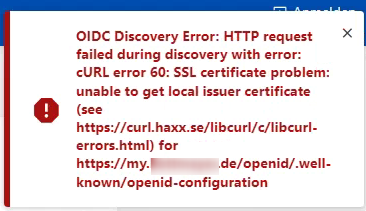
I changed my unbound config. I restarted the unbound service. Still get this error when trying to login.@buesching This is what I have in
/etc/unbound/unbound.conf.d/custom.conf:server: local-zone: smartserver.io typetransparent local-data: "my.smartserver.io A 172.18.0.1" local-data: "my.smartserver.io AAAA fd00:c107:d509::1"Then,
systemctl restart unboundTo verify (
44dea384c5b0is the bookstack container. you can dodocker psto find the bookstack container) :root@ubuntu-8gb-nbg1-1:~# docker exec -ti 44dea384c5b0 /bin/bash root@ff31e413-a6d2-4914-bccb-5eeef305839c:/app/code# host my.smartserver.io my.smartserver.io has address 172.18.0.1 my.smartserver.io has IPv6 address fd00:c107:d509::1The above confirms our unbound is working.
Then:
root@ff31e413-a6d2-4914-bccb-5eeef305839c:/app/code# curl https://my.smartserver.io/openid/.well-known/openid-configuration {"authorization_endpoint":"https://my.smartserver.io/openid/auth","claims_parameter_supported":false,"claims_supported":["sub","email","email_verified","family_name","given_name","locale","name","preferred_username","sid","auth_time","iss"],"code_challenge_methods_supported":["S256"],"grant_types_supported":["authorization_code","implicit","refresh_token"],"issuer":"https://my.smartserver.io/openid","jwks_uri":"https://my.smartserver.io/openid/jwks","authorization_response_iss_parameter_supported":true,"response_modes_supported":["form_post","fragment","query"],"response_types_supported":["code","id_token","id_token token","code id_token","code token","code id_token token","none"],"scopes_supported":["openid","offline_access","email","profile"],"subject_types_supported":["public"],"token_endpoint_auth_methods_supported":["client_secret_basic","client_secret_jwt","client_secret_post","private_key_jwt","none"],"token_endpoint_auth_signing_alg_values_supported":["HS256","RS256","PS256","ES256","EdDSA"],"token_endpoint":"https://my.smartserver.io/openid/token","id_token_signing_alg_values_supported":["RS256"],"pushed_authorization_request_endpoint":"https://my.smartserver.io/openid/request","request_parameter_supported":false,"request_uri_parameter_supported":false,"userinfo_endpoint":"https://my.smartserver.io/openid/me","claim_types_supported":["normal"]}We get OIDC response. Can you check where it fails above for you?
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login
