Mar 30 09:06:14 [3/30/2026, 16:06:14:098] [Server] Failed to detect IP from http://api.ipify.org 'getaddrinfo EAI_AGAIN api.ipify.org'
Mar 30 09:06:14 [3/30/2026, 16:06:14:101] [Server] Failed to detect IP from http://ipinfo.io/ip 'getaddrinfo EAI_AGAIN ipinfo.io'
Mar 30 09:06:14 [3/30/2026, 16:06:14:102] [Server] Failed to detect IP from http://ifconfig.me/ip 'getaddrinfo EAI_AGAIN ifconfig.me'
Mar 30 09:06:14 [3/30/2026, 16:06:14:103] [Server] Public IP detection failed 'All public IP detection services failed! Please check your network connection'
This looks like a network-related issue rather than something specific to MiroTalk.
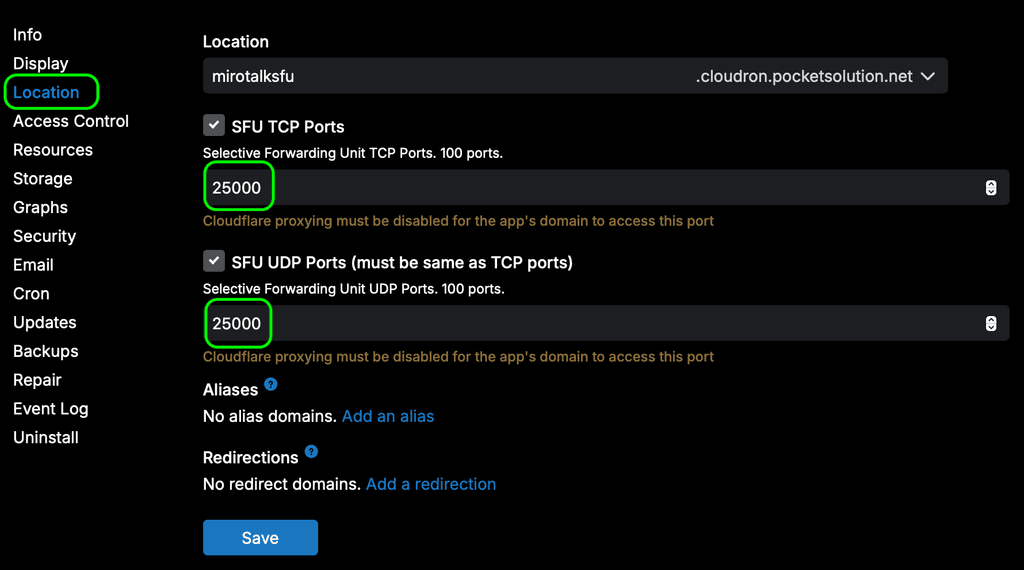
If SFU_ANNOUNCED_IP is not configured, the system will automatically rely on three external services to determine the instance’s public IPv4 address.
Is there a firewall or network filter in between that might be blocking traffic?
NOTE: As I can see, on Cloudron this is handled by the command in:
https://git.cloudron.io/packages/mirotalksfu-app/-/blob/main/start.sh#L39
If it fails (mean not set SFU_ANNOUNCED_IP), MiroTalk SFU uses an internal fallback mechanism that queries three external services in sequence to determine a valid public IPv4 address for the instance.


 Just a quick reminder to please purchase a license if you plan to use this in a commercial production environment.
Just a quick reminder to please purchase a license if you plan to use this in a commercial production environment.
 New Endpoint
New Endpoint Enable the Feature
Enable the Feature Quick Examples
Quick Examples Documentation
Documentation
 Also check Moderation settings
Also check Moderation settings MIROTALK ULTIMATE BUNDLE — LIMITED-TIME SALE — ENDS 23/01/2026!
MIROTALK ULTIMATE BUNDLE — LIMITED-TIME SALE — ENDS 23/01/2026! 


