-
@nebulon After I click authoirize on the pop up window, that window closes and focus returns to the wekan window but nothing happens at that point.
The sign in with OIDC button is disabled so it cannot be clicked again but the page doesn't respond.
We have our own root CA with a wild card signed certificate from this root ca used in cloudron.
I don't know the authentication flow but maybe there is a problem with the redirect back not trusting the endpoint it is posting something to.
Here is a video of the process:
-
@nebulon I should have thought to check, yes it is has the following error
Jul 31 10:59:21 {"line":"406","file":"oauth_server.js","message":"Error in OAuth Server: Failed to get token from OIDC https://my.cloudron.magnusonfinancial.com/openid/token: request to https://my.cloudron.magnusonfinancial.com/openid/token failed, reason: unable to verify the first certificate","time":{"$date":1690815561809},"level":"warn"} -
@nebulon If a cloudron domain DNS Provider is set to manual and a certificate is provided all apps that are loaded under that same domain should trust that certificate such that if you have cross app https connections, those connections will be trusted for all apps within that same domain at minimum.
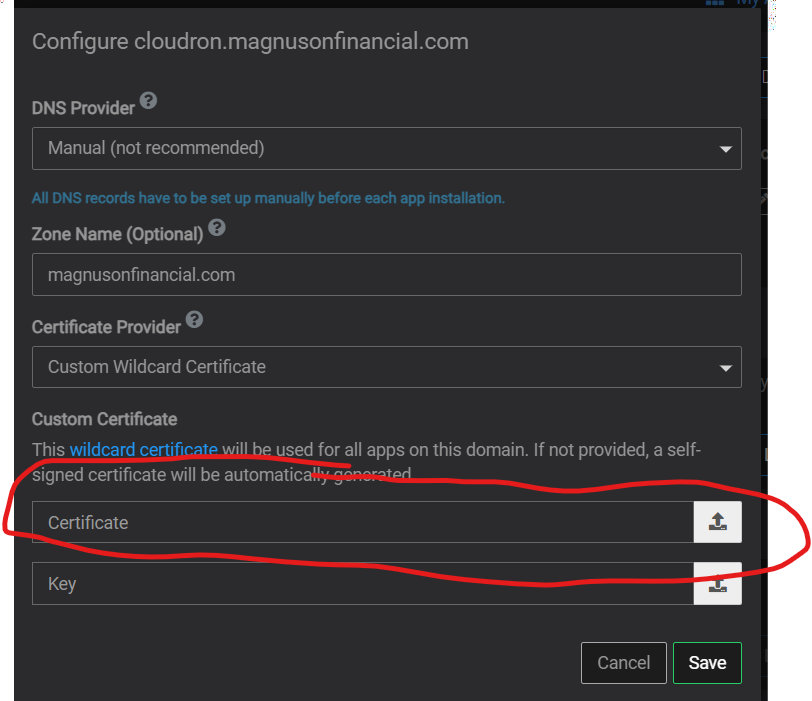
So assuming foo.crt was used in the form above then doing the below for each docker container so that they would each trust anything specified in foo.crt:ADD foo.crt /usr/local/share/ca-certificates/foo.crt RUN chmod 644/usr/local/share/ca-certificates/foo.crt &&update-ca-certificatesI didn't realize that this was related until we were looking this today I put this in as a request more generally a while back: https://forum.cloudron.io/topic/6381/if-the-custom-certificate-option-is-chosen-please-map-a-path-to-the-public-keys-into-each-container-s-ca-certificates-or-equivalent
I don't want to double dip but we recently had an issue with nextcloud that ended up being related to cloudron apps not trusting the manual certificate and I responded with something similar to @girish here: https://forum.cloudron.io/topic/9705/nextcloud-not-able-to-open-documents-using-the-onlyoffice-document-viewer-editor/37?_=1690813813008
-
Is there a way I can manually do the equivelant to doing the following in the app's docker config
ADD foo.crt /usr/local/share/ca-certificates/foo.crt RUN chmod 644/usr/local/share/ca-certificates/foo.crt &&update-ca-certificatesso that I can get the wekan app to trust the manually specified certificate being used by Cloudron for all its apps and for the dashboard url?
-
PS, this workflow with using
update-ca-certificatesI believe is relevant to containers based on debian/ubuntu but it might be a different workflow for whatever the cloudron base image is, trying to find documentation on what the cloudron base image uses to see if I can provide more correct information. -
@ChristopherMag Are you loading a self signed cert or a certificate signed by trusted CA? If it's the latter, everything should work. Can you confirm this aspect?
BTW, for the tests you mentioned in another comment, this is actually what we do. We have tests to login via browser automation. But these are tested against valid certs and not with self signed certs. I think it's not possible to support self signed certs reliably across apps especially for single sign on.
-
@girish We have our own self signed root-ca that is then signing the wildcard certificate so cloudron isn't using a self signed cert but it is using a certificate that is generated from a self signed root-ca.
I would love to not use a custom cert as it is a pain to manage loading it on all our client systems including mobile devices.
We use domains.google as our dns provider which is different than Google Cloud DNS and so it hasn't been one of the supported DNS providers in Cloudron.
I would love to not have this problem and maybe it is worth it to move to a new DNS domain registrar and DNS provider to get this accomplished as the "Google Domains" product has been sold off to Squarespace and I am not sure what the future will look like after they start to migrate customers over.
Maybe I can also split off our DNS hosting from our domain registrar.
The $12/year flat pricing with anonymization of the whois information, basic site redirection, support for wildcarding an entire subdomain so that any A record requests for hosts under that subdomain respond with the same ip address, all without upselling and spamming us was the motivation to move everything to domains.google.
The have been such a breath of fresh air compared to the godaddy's and networksolutions of the world.
Do any of the providers you support provide DNS for free as long as you register the domain name through them like domains.google does?
-
Actually you could use for example DigitalOcean DNS api only. It is free. You can keep your domain registrar and just set the nameservers from DigitalOcean there.
Being able to use LetsEncrypt certificates will surely spare you lots of side-effects and time.
-
@nebulon I will look into this and try to get this implemented, hopefully today, assuming that they handle all of our use cases.
Currently domains.google will redirect all requests from a domain that is an alias we have of another domain to the other domain both accross http and https and will preserving the path and query string parameters.
So a request for
https://www.mainalias.com/somepath?some=valueis redirected tohttps://www.main.com/somepath?some=valuewhich requires domains.google to get a free https certificate issued for mainaliasl.com, to run a webserver that has the ability to receive http requests, and then to set that webserver up to do the redirects, and they do this for free as a part of them being the registrar for that domain.As I write this I realize that maybe I just leave the dns servers as domains.google's dns servers for those domains and only change the name servers for the domain being used for our cloudron instance.
Thank you for helping me work through this and I will report back once I have gotten this setup with a test domain.
-
@girish @nebulon Thank you so much, I now have our domain registrar as domains.google but the authoritative name servers for our base domain and the subdomain we use to host cloudron as digital ocean and we now are able to use let's encrypt certs and login to wekan again!
The biggest trip up was the fact that domains.google defaults to returning its authoritative name servers for every subdomain of a domain it is hosting but digital ocean didn't so I needed to create name server records in the root domain configured in digital ocean that pointed back to digital ocean's name servers again before the subdomain which was also on digital ocean started working properly.
I did have to restart cloudron, sync dns, and renew all certs several times each as I worked through changing things and trying to get those changes to propagate, it at minimum took a reboot before the system stopped using the wildcard cert we had configured previously and started actually using the let's encrypt wildcard even though I had done multiple sync dns and renewa all certs before that.
This is a much better setup than before and it looks like it isn't going to cost anything more than what we were paying before, definitely a great solution and will hopefully stop us from hitting these weird issues with apps having trouble because they don't trust secure connections between each other.
Thank you both so much for helping me work through this!
-
@girish @nebulon Thank you so much, I now have our domain registrar as domains.google but the authoritative name servers for our base domain and the subdomain we use to host cloudron as digital ocean and we now are able to use let's encrypt certs and login to wekan again!
The biggest trip up was the fact that domains.google defaults to returning its authoritative name servers for every subdomain of a domain it is hosting but digital ocean didn't so I needed to create name server records in the root domain configured in digital ocean that pointed back to digital ocean's name servers again before the subdomain which was also on digital ocean started working properly.
I did have to restart cloudron, sync dns, and renew all certs several times each as I worked through changing things and trying to get those changes to propagate, it at minimum took a reboot before the system stopped using the wildcard cert we had configured previously and started actually using the let's encrypt wildcard even though I had done multiple sync dns and renewa all certs before that.
This is a much better setup than before and it looks like it isn't going to cost anything more than what we were paying before, definitely a great solution and will hopefully stop us from hitting these weird issues with apps having trouble because they don't trust secure connections between each other.
Thank you both so much for helping me work through this!
@ChristopherMag yes, having valid certs is the best way forward. Certs are also used in various non-HTTP protocols (irc, jabber, DoT, DoH etc) and most mobile apps will pretty much refuse to connect without valid certs. You are just fighting a battle which you will lose eventually. If not now, in the next update of the app.
Cloudron has support for self signed certs, but Cloudron started even before Let's Encrypt was a reality . These days all that code is just legacy. There is really no reason to use self signed certs for most purposes.
-
 N nebulon marked this topic as a question on
N nebulon marked this topic as a question on
-
 N nebulon has marked this topic as solved on
N nebulon has marked this topic as solved on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login