Hello @philkunz
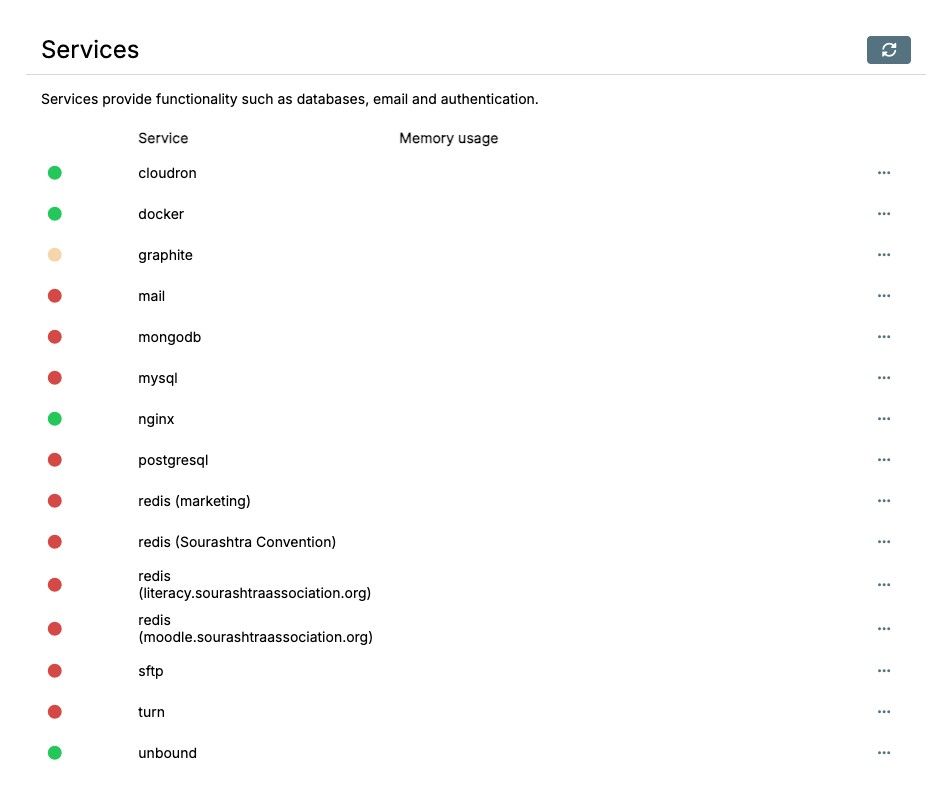
I can't tell what is accessing your MySQL Service, but if you use Cloudron in the default and not something out of the ordinary, it should be some app.
To get details about the hosts and connection errors, ssh into your Cloudron server, then run:
docker exec -it mysql bash -c 'mysql --user=root --password=$CLOUDRON_MYSQL_ROOT_PASSWORD --execute="SELECT * FROM performance_schema.host_cache"'
This will show all.
If you want to filter for the connection error specifically, run:
docker exec -it mysql bash -c 'mysql --user=root --password=$CLOUDRON_MYSQL_ROOT_PASSWORD --execute="SELECT HOST, SUM_CONNECT_ERRORS FROM performance_schema.host_cache WHERE SUM_CONNECT_ERRORS > 0;"'
it will create an output like:
mysql: [Warning] Using a password on the command line interface can be insecure.
+-----------------+--------------------+
| HOST | SUM_CONNECT_ERRORS |
+-----------------+--------------------+
| my-cloudron-dev | 1 |
+-----------------+--------------------+
You can also filter for the amount of auth errors with something like this:
docker exec mysql bash -c 'mysql --user=root --password=$CLOUDRON_MYSQL_ROOT_PASSWORD --execute="SELECT HOST, IP, SUM_CONNECT_ERRORS, COUNT_AUTHENTICATION_ERRORS FROM performance_schema.host_cache \G;"'
Which will return something like this:
*************************** 1. row ***************************
HOST: my-cloudron-dev
IP: fd00:c107:d509::1
SUM_CONNECT_ERRORS: 0
COUNT_AUTHENTICATION_ERRORS: 40
*************************** 2. row ***************************
HOST: mysql
IP: fd00:c107:d509::5
SUM_CONNECT_ERRORS: 0
COUNT_AUTHENTICATION_ERRORS: 17
*************************** 3. row ***************************
HOST: mysql
IP: 172.18.30.1
SUM_CONNECT_ERRORS: 0
COUNT_AUTHENTICATION_ERRORS: 1
*************************** 4. row ***************************
HOST: my-cloudron-dev
IP: 172.18.0.1
SUM_CONNECT_ERRORS: 1
COUNT_AUTHENTICATION_ERRORS: 2
There you can see I intentionally failed to connect many times from inside a Cloudron app by running:
for i in {1..20}; do mysql --user=${CLOUDRON_MYSQL_USERNAME} --password=WRONGPASSWORD --host=${CLOUDRON_MYSQL_HOST} ${CLOUDRON_MYSQL_DATABASE}; done
When running this again from inside a Cloudron app, I can run the above MySQL query again and can see:
*************************** 1. row ***************************
HOST: my-cloudron-dev
IP: fd00:c107:d509::1
SUM_CONNECT_ERRORS: 0
COUNT_AUTHENTICATION_ERRORS: 60
Is now 60 and was before 40.
If this value keeps rising, without you doing anything manually.
There is some app that is failing to connect to the MySQL service for some reason.
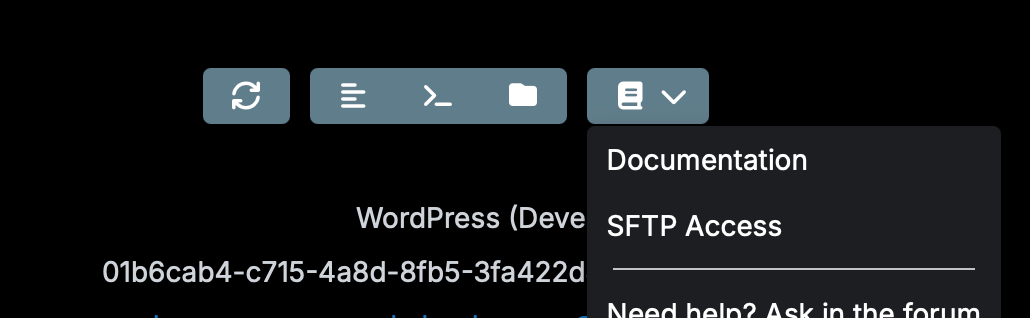
My first suspect would be some WordPress developer app or a restored app that has old credentials from before the restore.