Where is the coturn config located?
-
I am trying to resolve my issues with the TURN server not working (across multiple apps) for me. It seems I just get errors saying local ports are blocked. I have port forwarded.
Where would I find the coturn config for Cloudron? the one I found in /etc/ seems to have everything commented out.
-
@atrilahiji that just means it's using defaults, no?
otherwise it's in a container?
When I had TURN issues it was not with Cloudron, but with router or App. And since Apps are managed config, they should be good.
-
@atrilahiji we can't guess as to what app, network config and where clients are coming from.. or logs with errors.
-
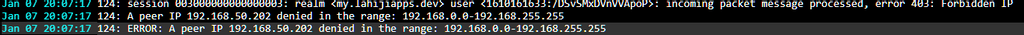
@atrilahiji that looks like an error in NC Talk.
I have a Cloudron with a similar setup and once the v6 upgrade happened our NC:T went down. We just needed the new ports added to the router for STUN & TURN.
-
@robi Those logs are for the TURN service in the services page on my cloudron btw. So I get the exact same thing when I try a video chat with Kopano Meet. These are my forwaded ports for the same IP that is apparently being blocked:
3478,3479,5349,5350,49152:65535/tcp
3478,3479,5349,5350,49152:65535/udp -
@atrilahiji I see..
can you find the process and trace it to a container?I have to run atm, but would dig into the CL TURN docs and see how or why they restrict the private networks if that's where it's blocked.
-
@atrilahiji So the turn addon is configured as per https://github.com/coturn/coturn/blob/master/examples/etc/turnserver.conf to have the following ports:
listening-port=3478 tls-listening-port=5349 min-port=50000 max-port=51000We have also included a section for preventing some attack, which I think is what you may hit?
# https://www.rtcsec.com/2020/04/01-slack-webrtc-turn-compromise/ no-multicast-peers denied-peer-ip=0.0.0.0-0.255.255.255 denied-peer-ip=10.0.0.0-10.255.255.255 denied-peer-ip=100.64.0.0-100.127.255.255 denied-peer-ip=127.0.0.0-127.255.255.255 denied-peer-ip=169.254.0.0-169.254.255.255 denied-peer-ip=127.0.0.0-127.255.255.255 denied-peer-ip=172.16.0.0-172.31.255.255 denied-peer-ip=192.0.0.0-192.0.0.255 denied-peer-ip=192.0.2.0-192.0.2.255 denied-peer-ip=192.88.99.0-192.88.99.255 denied-peer-ip=192.168.0.0-192.168.255.255 denied-peer-ip=198.18.0.0-198.19.255.255 denied-peer-ip=198.51.100.0-198.51.100.255 denied-peer-ip=203.0.113.0-203.0.113.255 denied-peer-ip=240.0.0.0-255.255.255.255Those IPs are anyways no public IPs and thus would not help you to achieve connectivity through it as far as I understand.
-
@atrilahiji The config is in
/run/turnserver/turnserver.confinside the container -
-
@atrilahiji computer = server, so yes. clients no.
-
@atrilahiji Yes, same box. it's actually a nested virtualized server and the host is a client.
ISP Router ports forward directly to the server for this. -
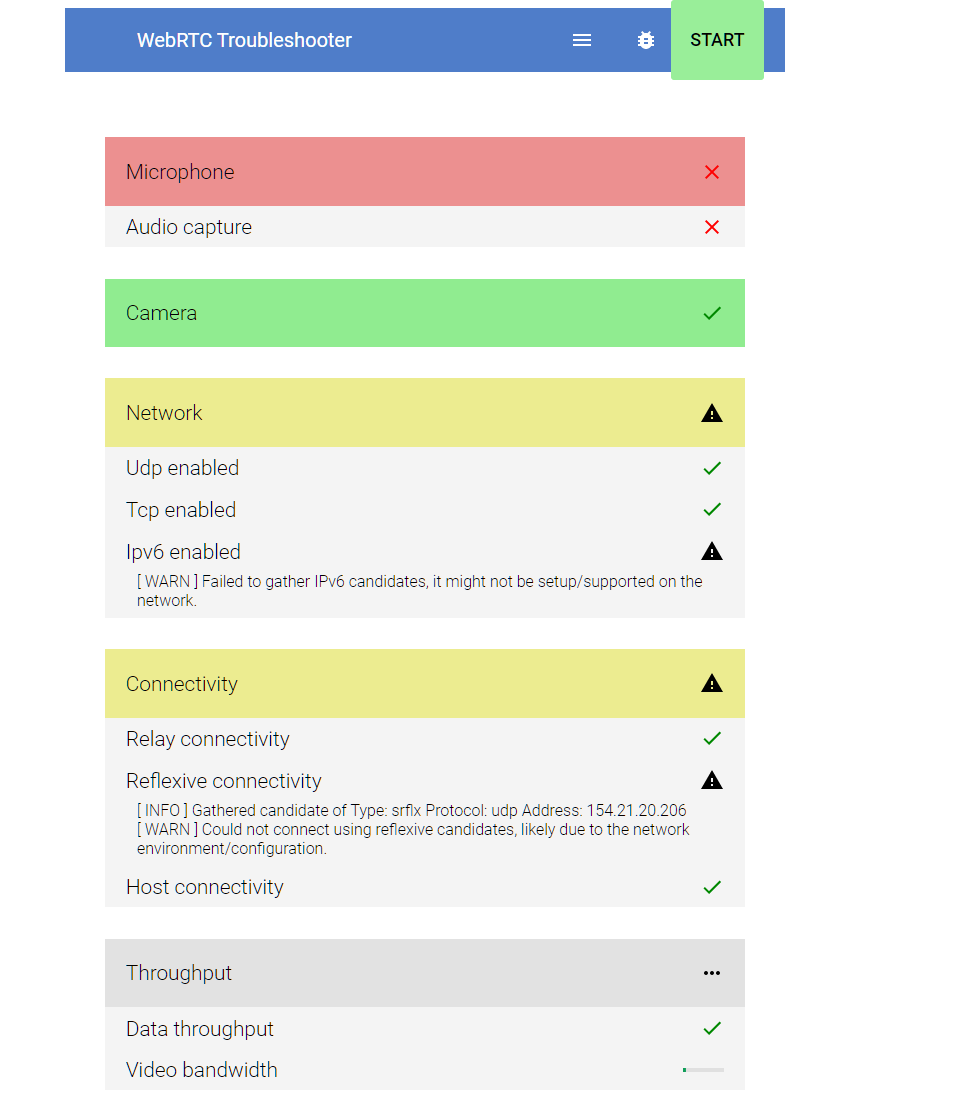
Huh so I am back on the debugging train here. I do seem to fail the Reflexive connectivity test here O_OAlso, I should point out that I use Adguard Home on my router, which is also what connects to my cloudron. Would that cause any problems?
But its weird because it seems to work between my phone on data and my desktop (on the same network as my cloudron) but not between my someone in toronto and my desktop.
I remember there was a change related to this slated for a release @girish. Is this true? I'm really not sure what else I can do here O_O
EDIT: Seems like my investigations are going nowhere

I assumed it might have to do with this commit but if it works for Robi in the same scenario I've got nothing else I can think of trying: https://git.cloudron.io/cloudron/box/-/commit/6adf5772d8f871eae98ad5f5ffdbed7098bac214
-
@atrilahiji No Adguard in our picture so try disabling it temporarily.
-
Ugh no luck...