Hello @günter
@Günter said:
I restarted the "Filemanager" service, I restarted the whole machine. Via Web-CLI I can access the /app/data directories without any issues. When the Filemanager is opened on a Volume ("Volumes" -> "⋅⋅⋅" per volume -> "File manager") it also works fine and shows the content of all the apps in that volume.
Just to confirm:
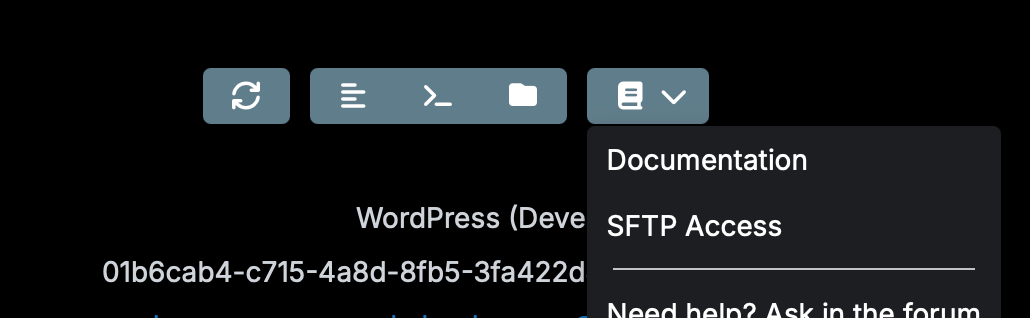
view from web terminal of an app, working
view from web file manager over the volume view https://my.$DOMAIN.$TLD/#/volumes, works
view from web file manager from the app, still not working?
I tried to reproduce this with these steps:
attaching a new disk to my Cloudron server
made the disk a ext4 with mkfs.ext4 "/dev/disk/by-id/scsi-0Linode_Volume_dev-volume"
in the dashboard created the volume as ext4, named it dev-volume
moved a fresh LAMP app default storage to Volume - dev-volume Subdirectory lamp
could view the files with the Web File Manager from the app, volume and web terminal view
confirmed by creating a dev.txt with the Web File Manager and checking with ssh if the file exists on the volume
also tested without a Subdirectory
Was not able to reproduce this.
If the issue still persists, please contact support@cloudron.io so we can analyse this issue more detailed.