How to configure LDAP in Discourse?
-
This was previously posted in the Discourse App wishlist topic.
I'm trying to add LDAP support myself. I've added the ldap addon to the package manifest, built and installed it. I've also installed the discourse-ldap-auth plugin. It sort of works!

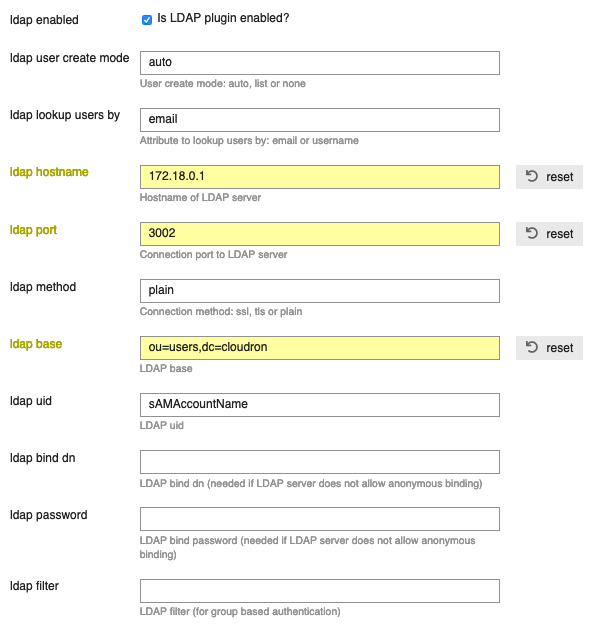
Here are the settings I could figure out myself:
Remaining issues:
- For
invite-onlyforums that only want LDAP, that setting has to be turned off. Otherwise LDAP users can't authenticate. The feature can still be achieved by- disabling
enable local logins - disablling
enable local logins via email - reenable
allow new registrations(Brings back the Sign up button, but luckily (!?) it leads to LDAP login too.
- disabling
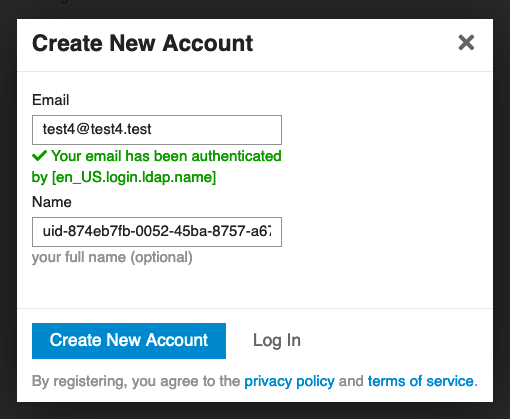
- Accounts aren't automatically created. (Not possible currently)
- I don't know what
en_US.login.ldap.nameis or how to map it/fix it. - I don't know how to map the suggested username to the Cloudron username upon Discourse account creation. I would also want to lock it.
- I don't know any other LDAP settings, I just ripped them from the Wordpress LDAP integration settings

- LDAP sign-in UI looks off-brand and dodgy, possibly signalling phishing attempt for some users.
Any help appreciated!
- For
-
If the LDAP add-on is enabled for the app at least, it should be able to bind and authenticate even if it means manually copying credentials. I may have to steal them from another app (bad!) in the mean time though since I'm getting complaints from users
-
@jimcavoli said in How to configure LDAP in Discourse?:
fork and update this plugin to work more automatically
Do you mean that you would be able to address the non-automatic account creation?
-
@jimcavoli said in How to configure LDAP in Discourse?:
fork and update this plugin to work more automatically
Do you mean that you would be able to address the non-automatic account creation?
@yusf I'm not gonna say yes at this point since syncing requires some sort of cron-like setup and I'm just not sure how involved that would be - I mostly meant reading those settings in from the LDAP add-on without having to copy them into the admin UI from the app's console.
I wouldn't rule it out, but if we could get that to be the only outstanding "issue" it strikes me that would be substantial progress for a start
-
I see. I don't know where the plugin data is stored but I suppose the official package can be modified to include the LDAP addon, the plugin and its settings.
My personal incentive however, is to improve the experience for users (wrt the bullets above). Package automation can come later.
-
Gets a little technical about ruby and how discourse manages the plugins, but that all sort of goes hand-in-hand. Depending how the next day or two go, I'll see about doing something that we can use in order to keep the conversation moving and have a base to tackle some of those features from. Appreciate the context of your goals; I'll bear that in mind when the code starts flying

-
Gets a little technical about ruby and how discourse manages the plugins, but that all sort of goes hand-in-hand. Depending how the next day or two go, I'll see about doing something that we can use in order to keep the conversation moving and have a base to tackle some of those features from. Appreciate the context of your goals; I'll bear that in mind when the code starts flying

@jimcavoli Did any code start flying?

-
@jimcavoli Did any code start flying?

-
@girish It was not. As mentioned earlier I did some light digging into the issue but as you can see in this issue that is where it's at currently.
I figured there's no harm in enabling the Cloudron LDAP addon in the package but I realize that as maintainer you may have another view on that matter.
-
@yusf If I understand the current situation, if the LDAP plugin is enabled:
- User logs in.
- User sees a screen to 'create new account'. User has to just click through.
Is this the case? If so, that does not seem like a major issue.
-
@yusf To keep you updated, I looked into this a bit further. The issue is that when we add ldap as addon, Cloudron UI selects this as the default. For an app like discourse, using LDAP is uncommon since it's mostly a publicly forum use case.
I think before we add LDAP support to nodebb/discourse etc, we need to fix Cloudron to support "dynamic addons". This way one can toggle LDAP support on/off whenever they want. That's the best way to fix this. Otherwise, I suspect, people will blindly install Discourse with LDAP, then disable LDAP inside Discourse and this will only lead to problems (since in Cloudron packages currently we assume that LDAP support is never removed like that inside an app).
-
@yusf To keep you updated, I looked into this a bit further. The issue is that when we add ldap as addon, Cloudron UI selects this as the default. For an app like discourse, using LDAP is uncommon since it's mostly a publicly forum use case.
I think before we add LDAP support to nodebb/discourse etc, we need to fix Cloudron to support "dynamic addons". This way one can toggle LDAP support on/off whenever they want. That's the best way to fix this. Otherwise, I suspect, people will blindly install Discourse with LDAP, then disable LDAP inside Discourse and this will only lead to problems (since in Cloudron packages currently we assume that LDAP support is never removed like that inside an app).
@girish Seems like an apt solution to the problem. Thanks for looking into it.
For what it’s worth I’m often faced with the opposite use-case: some group need internal forum software, apart from other Cloudron services. So I’m interested in doing the same thing with NodeBB.
-
@yusf To keep you updated, I looked into this a bit further. The issue is that when we add ldap as addon, Cloudron UI selects this as the default. For an app like discourse, using LDAP is uncommon since it's mostly a publicly forum use case.
I think before we add LDAP support to nodebb/discourse etc, we need to fix Cloudron to support "dynamic addons". This way one can toggle LDAP support on/off whenever they want. That's the best way to fix this. Otherwise, I suspect, people will blindly install Discourse with LDAP, then disable LDAP inside Discourse and this will only lead to problems (since in Cloudron packages currently we assume that LDAP support is never removed like that inside an app).
@girish said in How to configure LDAP in Discourse?:
For an app like discourse, using LDAP is uncommon since it's mostly a publicly forum use case.
Even in those cases it'd still be nice to have LDAP, like we can in Rocket.Chat right now, i.e. Cloudron uses can use LDAP to login to Rocket.Chat using their Clourdon credentials, and non-Cloudron users can just register and login as normal too.
I'd like the same UX for Discourse too, best of both worlds!

-
@yusf To keep you updated, I looked into this a bit further. The issue is that when we add ldap as addon, Cloudron UI selects this as the default. For an app like discourse, using LDAP is uncommon since it's mostly a publicly forum use case.
I think before we add LDAP support to nodebb/discourse etc, we need to fix Cloudron to support "dynamic addons". This way one can toggle LDAP support on/off whenever they want. That's the best way to fix this. Otherwise, I suspect, people will blindly install Discourse with LDAP, then disable LDAP inside Discourse and this will only lead to problems (since in Cloudron packages currently we assume that LDAP support is never removed like that inside an app).
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login