Firezone - FOSS noconf Mesh VPN using Wireguard, alternative to ZeroTier, Tailscale, OmniEdge, Netmaker etc
-
- https://www.firezone.dev/
- https://github.com/firezone/firezone
- https://docs.firezone.dev/deploy
- https://docs.firezone.dev/deploy/docker/
- https://github.com/firezone/fz_docker
- https://docs.firezone.dev/authenticate/oidc/keycloak/
- https://alternativeto.net/software/firezone/about/
- https://alternativeto.net/software/firezone/?license=opensource
- https://forum.cloudron.io/topic/7560/omniedge-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-etc
- https://forum.cloudron.io/topic/7563/tailscale-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-etc
- https://forum.cloudron.io/topic/7565/netmaker-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-etc
- https://forum.cloudron.io/topic/7571/netbird-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-netmaker-etc
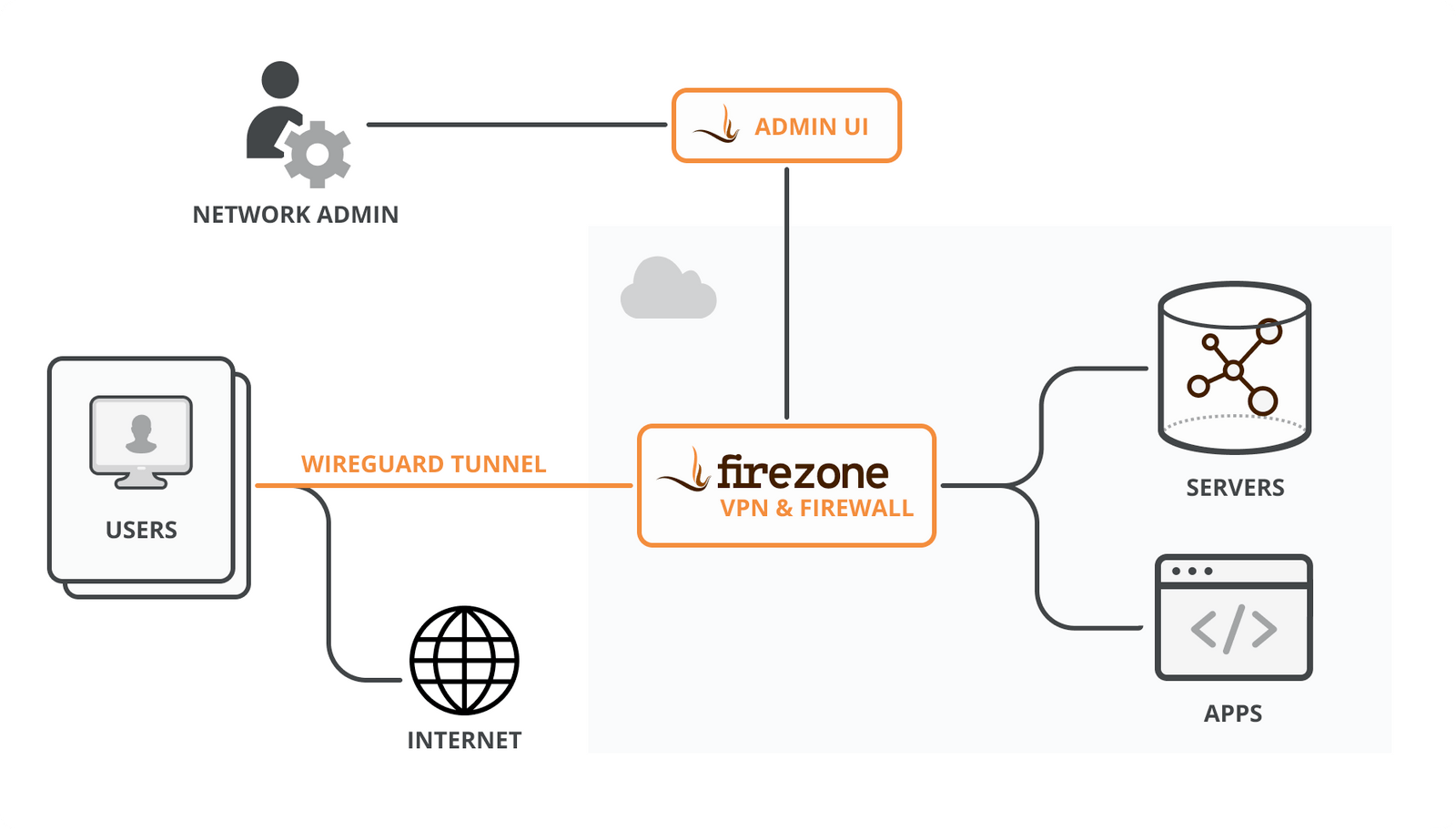
Self-hosted secure remote access
Firezone is an open-source VPN and firewall server built on WireGuard to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.
to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.sudo -E bash -c "$(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/install.sh)"
Uses the standard Wireguard clients for all platforms, and the QR code generation looks good for making the setups easy enough for non-technical users.
Looks like it supports Keycloak, so may interest @nj
Common Use Cases
NAT Gateway (Static IP)
Restrict access for a self-hosted web app to a single whitelisted static IP running Firezone. (a highly recommended additional layer of protection for self-hosted apps that don't need to be exposed to on public IPs).
Reverse Tunnels
Enable an administrator to access a server, container, or machine that is normally behind a NAT or firewall.
Split Tunnels
Only traffic to defined IP ranges will be routed through the VPN server.
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
- https://www.firezone.dev/
- https://github.com/firezone/firezone
- https://docs.firezone.dev/deploy
- https://docs.firezone.dev/deploy/docker/
- https://github.com/firezone/fz_docker
- https://docs.firezone.dev/authenticate/oidc/keycloak/
- https://alternativeto.net/software/firezone/about/
- https://alternativeto.net/software/firezone/?license=opensource
- https://forum.cloudron.io/topic/7560/omniedge-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-etc
- https://forum.cloudron.io/topic/7563/tailscale-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-etc
- https://forum.cloudron.io/topic/7565/netmaker-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-etc
- https://forum.cloudron.io/topic/7571/netbird-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-netmaker-etc
Self-hosted secure remote access
Firezone is an open-source VPN and firewall server built on WireGuard to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.
to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.sudo -E bash -c "$(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/install.sh)"
Uses the standard Wireguard clients for all platforms, and the QR code generation looks good for making the setups easy enough for non-technical users.
Looks like it supports Keycloak, so may interest @nj
Common Use Cases
NAT Gateway (Static IP)
Restrict access for a self-hosted web app to a single whitelisted static IP running Firezone. (a highly recommended additional layer of protection for self-hosted apps that don't need to be exposed to on public IPs).
Reverse Tunnels
Enable an administrator to access a server, container, or machine that is normally behind a NAT or firewall.
Split Tunnels
Only traffic to defined IP ranges will be routed through the VPN server.
@marcusquinn not sure I know enough yet to judge, but I’m drawn more to this one out of the various options posted.
Just my initial unqualified 2p -
@marcusquinn not sure I know enough yet to judge, but I’m drawn more to this one out of the various options posted.
Just my initial unqualified 2p -
- https://www.firezone.dev/
- https://github.com/firezone/firezone
- https://docs.firezone.dev/deploy
- https://docs.firezone.dev/deploy/docker/
- https://github.com/firezone/fz_docker
- https://docs.firezone.dev/authenticate/oidc/keycloak/
- https://alternativeto.net/software/firezone/about/
- https://alternativeto.net/software/firezone/?license=opensource
- https://forum.cloudron.io/topic/7560/omniedge-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-etc
- https://forum.cloudron.io/topic/7563/tailscale-decentralised-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-etc
- https://forum.cloudron.io/topic/7565/netmaker-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-etc
- https://forum.cloudron.io/topic/7571/netbird-foss-noconf-mesh-vpn-using-wireguard-alternative-to-zerotier-tailscale-omniedge-netmaker-etc
Self-hosted secure remote access
Firezone is an open-source VPN and firewall server built on WireGuard to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.
to be stable, performant, and lightweight. Deploy in minutes on your own infrastructure.sudo -E bash -c "$(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/install.sh)"
Uses the standard Wireguard clients for all platforms, and the QR code generation looks good for making the setups easy enough for non-technical users.
Looks like it supports Keycloak, so may interest @nj
Common Use Cases
NAT Gateway (Static IP)
Restrict access for a self-hosted web app to a single whitelisted static IP running Firezone. (a highly recommended additional layer of protection for self-hosted apps that don't need to be exposed to on public IPs).
Reverse Tunnels
Enable an administrator to access a server, container, or machine that is normally behind a NAT or firewall.
Split Tunnels
Only traffic to defined IP ranges will be routed through the VPN server.
@marcusquinn Awesome find!
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
@marcusquinn Awesome find!
@micmc does that work with dynamic IPs as well?
-
@micmc does that work with dynamic IPs as well?
@necrevistonnezr My complete guess is the broker service needs a fixed IP or domain mapped to a dynamic DNS service, but that clients shouldn't need fixed IPs.
-
F fbartels referenced this topic on
-
Docker deployment now preferred: https://docs.firezone.dev/deploy/docker/
-
Keycloak integration: https://docs.firezone.dev/authenticate/oidc/keycloak/
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
Having this on Cloudron would be fantastic
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
Thanks to @marcusquinn for helping me find this request. There is at the moment an early access beta test for version 1.0 available here. Your contact details would be needed:
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login