NetBird - FOSS noconf Mesh VPN using Wireguard, alternative to ZeroTier, Tailscale, OmniEdge, Netmaker etc
-
NetBird author is here.
Thanks, @marcusquinn, for posting about NetBird!
Thank you, @privsec, for the kind feedback.
I see that there is quite an interest. Feel free to ask me any questions

@braginini Would you be open to helping package this for Cloudron?
-
N necrevistonnezr referenced this topic on
-
F fbartels referenced this topic on
-
NetBird author is here.
Thanks, @marcusquinn, for posting about NetBird!
Thank you, @privsec, for the kind feedback.
I see that there is quite an interest. Feel free to ask me any questions

-
Works with Keycloak too: https://netbird.io/docs/integrations/identity-providers/self-hosted/using-netbird-with-keycloak
-
 G girish referenced this topic on
G girish referenced this topic on
-
T timka referenced this topic on
-
 M marcusquinn referenced this topic on
M marcusquinn referenced this topic on
-
Revisited all of these alternatives.
Netbird is the clear winner for me. Has my recommendation!
-
1st draft packaging this, if anyone that know's more wants to test:
-
Update on the Cloudron NetBird package
The packaging scaffold at https://github.com/marcusquinn/cloudron-netbird-app is fairly complete -- it uses the combinednetbird-serverbinary behind an internal nginx that consolidates all the path-based routing (gRPC, WebSocket, REST API, dashboard) onto a single HTTP port for Cloudron's reverse proxy.
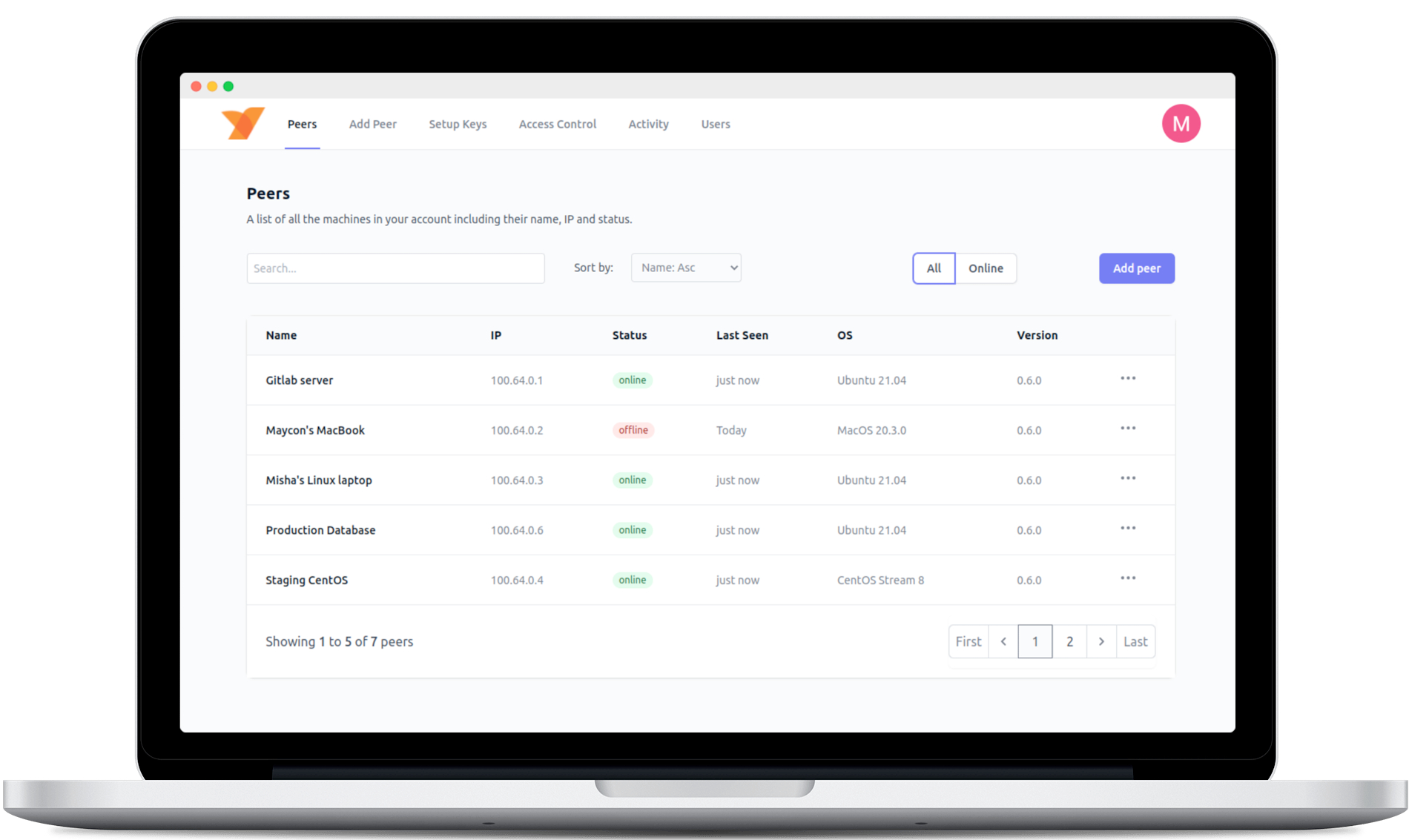
What works (in theory -- needs real-world testing):- Management API, Signal, Relay, STUN, and Dashboard all in one container
- Cloudron SSO via the OIDC addon
- Cloudron's built-in TURN server for NAT traversal relay
- PostgreSQL via Cloudron addon
- Backup/restore of all persistent state
The one feature that can't work on Cloudron: NetBird's Reverse Proxy (v0.65+)
This is NetBird's newer feature that exposes internal services on mesh peers to the public internet with automatic TLS. It requires Traefik with TLS passthrough -- the NetBird proxy container needs to terminate TLS itself. Cloudron's nginx terminates TLS before traffic reaches the app, so there's no way to pass through the raw TLS connection that NetBird's proxy needs.
I looked at whetheralpine/socat(TCP socket forwarder) could bridge this gap, but it can't -- the problem is Layer 7 (HTTP path routing, gRPC protocol handling, TLS termination order), not Layer 4 (TCP forwarding). socat only does port-to-port TCP forwarding and has no understanding of HTTP paths, gRPC, or WebSocket upgrade headers.
This doesn't affect the core VPN functionality at all -- peer-to-peer WireGuard tunnels, NAT traversal, access control, DNS, network routes, and the management dashboard all work fine without it. The reverse proxy is an optional add-on for publicly exposing internal services.
What's needed next:
- Testing on a real Cloudron instance (I haven't done this yet -- the packaging is based on docs and the combined container architecture)
- Verifying the internal nginx correctly handles the gRPC h2c proxying that Signal and Management need
- End-to-end OIDC flow testing with Cloudron SSO
- TURN relay testing for peers behind strict NAT
If anyone wants to help test, the repo has a full testing checklist in the README. Would be great to get this into the Cloudron App Store.
feedback welcome!
-
Great work @marcusquinn
Will try to test it out, been wanting NetBird, currently running it on a separate VPS
I ran into similar issues about routing of traffic when I was packaging Agate+. But I don’t recall the solution (and may not be a solution) - will try to check it out.
-
-
Testing on a real Cloudron instance (I haven't done this yet -- the packaging is based on docs and the combined container architecture)
I don't know how this is possible - I always need to do multiple builds to get a working package.
I started building from @marcusquinn repo.
I needed to make some changes. Currently app builds and installs but have hit a circular dependency ("Catch-22") regarding authentication.The Goal: Configure NetBird to use Cloudron's OIDC service as its Identity Provider.
The Problem:
- Configuration requires Login: To add Cloudron OIDC as an IdP, I need to log in to the NetBird dashboard (or use the API, which requires a token).
- Initial Login requires Embedded Dex: Since Cloudron OIDC isn't configured yet, I must use the embedded Dex IdP for the first login.
- Embedded Dex Fails: The embedded IdP is configured strictly according to the "combined server" docs (v0.36+). The dashboard loads, redirects to the embedded auth flow, but fails at the final step:
- POST /oauth2/token returns 401 Unauthorized .
- Browser console shows: storage[oidc.login.default] is empty and Token request failed .
- Logs show no specific server-side error, just the 401.
The Catch-22: I cannot log in (via embedded Dex) to configure the external IdP (Cloudron OIDC). I cannot configure the external IdP via files/env vars to bypass the broken embedded login.
I will try a hack to get past this.
-
Starting again, fresh start.
Will update. -
Parking this for now - can't get past auth errors, even stripping out any OIDC and just using the embedded Dex user management.
Will resume at some point because Netbird is very cool, works well for me via separately-hosted docker compose, and would be good to have on Cloudron.
But other priorities push Netbird down the list. -
Parking this for now - can't get past auth errors, even stripping out any OIDC and just using the embedded Dex user management.
Will resume at some point because Netbird is very cool, works well for me via separately-hosted docker compose, and would be good to have on Cloudron.
But other priorities push Netbird down the list.@timconsidine thanks for testing. Refactored so OICD is an optional extra, plus other changes to the whole approach. README should explain.
-
@timconsidine thanks for testing. Refactored so OICD is an optional extra, plus other changes to the whole approach. README should explain.
@marcusquinn I tried similar approach - simplify to just Netbird and embedded Dex. But that wasn't enough.
Will try again shortly with fresh brain.
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login