Our server is hacked: foreign addresses in china, finland, france etc
-
@LoudLemur yes full disk images are regularly as big as the disk it self.
So if you got a 1TB disk the Disk Image will be 1TB.
Yes you could cut empty space which is unused.When a system is compromised, normally you shutdown the system, create a disk image and then format the server and setup new.
Then this disk image can be used for later analytics.@BrutalBirdie on a vps, is a server snapshot the equivalent to a full disk image and can it be used for analytics?
-
@BrutalBirdie on a vps, is a server snapshot the equivalent to a full disk image and can it be used for analytics?
@humptydumpty Should be.
If you can create a server from it or attach it to a different server, then sure. -
@humptydumpty Should be.
If you can create a server from it or attach it to a different server, then sure. -
@andreasdueren I am running all cloudron servers with root on complete lockdown.
This even blocks default support access for the staff, if you enabled it.I also use normal ssh keys for the designated sudo user and also
ed25519-skandecdsa-skssh keys for 2FA via Yubikey.
This works with no issues.@BrutalBirdie said in Our server is hacked: foreign addresses in china, finland, france etc:
@andreasdueren I am running all cloudron servers with root on complete lockdown.
This even blocks default support access for the staff, if you enabled it.
I also use normal ssh keys for the designated sudo user and also ed25519-sk and ecdsa-sk ssh keys for 2FA via Yubikey.
This works with no issues.Would you mind sharing the steps you took? I'd like to try that out on a test server
-
@BrutalBirdie said in Our server is hacked: foreign addresses in china, finland, france etc:
@andreasdueren I am running all cloudron servers with root on complete lockdown.
This even blocks default support access for the staff, if you enabled it.
I also use normal ssh keys for the designated sudo user and also ed25519-sk and ecdsa-sk ssh keys for 2FA via Yubikey.
This works with no issues.Would you mind sharing the steps you took? I'd like to try that out on a test server
For everyone interested we (we as in, my company and me) also offer Cloudron hosting as as a service.
So I can't reveal my whole hand so please be understanding
so please be understanding 
But what you are asking about is pretty simple:
Create a user with sudo permissions and add your ssh public key to that user (don't lose the password for that user since you will need it for sudo)
I also disable all ssh access with password, since this only opens the window for brute force attempts
Depends on the lock down wanted, you can also disable the root login via
/etc/passwdby setting the login shell to/sbin/nologinlooks something like this:root:x:0:0:root:/root:/sbin/nologinThen, even if you try a
sudo su -you get this:This account is currently not available.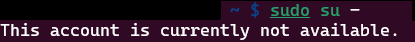
But since you can edit the/etc/passwdwith sudo access (unless you lock down the system even further) this can be a bit snake oily.
There is much more going on in my servers, but since we deploy everything via. Ansible I don't need to keep track of ever single detail, since its infrastructure as a code, I can just read up.
Login tracking, Log Tracking, Monitoring yada yada yada.If a system farts, I get a message.
I hope this shares some insights.
A step by step guide on how to lock down the root user would simply be me copy pasting google searches.
When it's about Linux security you can do sooooo much: https://wiki.archlinux.org/title/security
there is also a good section on "restricting root"
EDIT:
Maybe I can do a step by step guide in the forum when I got some spare time.

But right now its a bit late and I am lazy
-
For everyone interested we (we as in, my company and me) also offer Cloudron hosting as as a service.
So I can't reveal my whole hand so please be understanding
so please be understanding 
But what you are asking about is pretty simple:
Create a user with sudo permissions and add your ssh public key to that user (don't lose the password for that user since you will need it for sudo)
I also disable all ssh access with password, since this only opens the window for brute force attempts
Depends on the lock down wanted, you can also disable the root login via
/etc/passwdby setting the login shell to/sbin/nologinlooks something like this:root:x:0:0:root:/root:/sbin/nologinThen, even if you try a
sudo su -you get this:This account is currently not available.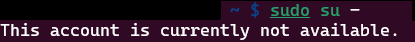
But since you can edit the/etc/passwdwith sudo access (unless you lock down the system even further) this can be a bit snake oily.
There is much more going on in my servers, but since we deploy everything via. Ansible I don't need to keep track of ever single detail, since its infrastructure as a code, I can just read up.
Login tracking, Log Tracking, Monitoring yada yada yada.If a system farts, I get a message.
I hope this shares some insights.
A step by step guide on how to lock down the root user would simply be me copy pasting google searches.
When it's about Linux security you can do sooooo much: https://wiki.archlinux.org/title/security
there is also a good section on "restricting root"
EDIT:
Maybe I can do a step by step guide in the forum when I got some spare time.

But right now its a bit late and I am lazy
@BrutalBirdie I never had password access enabled on my servers in the first place but I'm interested in locking it down a little more that's why I asked. Thank you!
-
For everyone interested we (we as in, my company and me) also offer Cloudron hosting as as a service.
So I can't reveal my whole hand so please be understanding
so please be understanding 
But what you are asking about is pretty simple:
Create a user with sudo permissions and add your ssh public key to that user (don't lose the password for that user since you will need it for sudo)
I also disable all ssh access with password, since this only opens the window for brute force attempts
Depends on the lock down wanted, you can also disable the root login via
/etc/passwdby setting the login shell to/sbin/nologinlooks something like this:root:x:0:0:root:/root:/sbin/nologinThen, even if you try a
sudo su -you get this:This account is currently not available.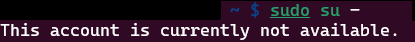
But since you can edit the/etc/passwdwith sudo access (unless you lock down the system even further) this can be a bit snake oily.
There is much more going on in my servers, but since we deploy everything via. Ansible I don't need to keep track of ever single detail, since its infrastructure as a code, I can just read up.
Login tracking, Log Tracking, Monitoring yada yada yada.If a system farts, I get a message.
I hope this shares some insights.
A step by step guide on how to lock down the root user would simply be me copy pasting google searches.
When it's about Linux security you can do sooooo much: https://wiki.archlinux.org/title/security
there is also a good section on "restricting root"
EDIT:
Maybe I can do a step by step guide in the forum when I got some spare time.

But right now its a bit late and I am lazy
@BrutalBirdie said in Our server is hacked: foreign addresses in china, finland, france etc:
step by step guide in the forum when I got some spare time.
I don't think you "need" to do this. There are sooo many tutorials out there, easily findable, about how to secure and lockdown a server. What you described is even the most base-level steps, but so many people don't even do that! All anyone has to do is google those terms, "secure and lock down a server" and then choose the most reliable results. Anyone who needs this can find the info and put the steps into place way before you will find time to do a write-up.
-
@BrutalBirdie said in Our server is hacked: foreign addresses in china, finland, france etc:
step by step guide in the forum when I got some spare time.
I don't think you "need" to do this. There are sooo many tutorials out there, easily findable, about how to secure and lockdown a server. What you described is even the most base-level steps, but so many people don't even do that! All anyone has to do is google those terms, "secure and lock down a server" and then choose the most reliable results. Anyone who needs this can find the info and put the steps into place way before you will find time to do a write-up.
@scooke I'm not so much concerned as to achieve hardened security on my server but more not having those measure interfere with cloudron and create problems. For example I would like to add 2FA with Yubikey but that involves installing packages which we are discouraged from doing. That's why I asked for his setup.
-
@scooke I'm not so much concerned as to achieve hardened security on my server but more not having those measure interfere with cloudron and create problems. For example I would like to add 2FA with Yubikey but that involves installing packages which we are discouraged from doing. That's why I asked for his setup.
@andreasdueren I'd be cautious about implementing it then. Cloudron hardens your server enough - doing more by installing more software, which is NOT recommended, will only lead to problems, especially if you don't already have a deep enough understanding of what is happening. It seems to be that @BrutalBirdie's gang knows their stuff (they're using Ansible to install Cloudron??? Yeah, that is next level coding there). Of course, they may also be paying for the Enterprise level of service (I'm not asking btw, no need to respond to that @BrutalBirdie ) so if they have hassles then I suppose it's fine for them to get help beyond typical Cloudron support, especially if they are doing more to their servers than what Cloudron themselves advise.
-
 G girish marked this topic as a question on
G girish marked this topic as a question on
-
 G girish has marked this topic as solved on
G girish has marked this topic as solved on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login