-
Autodiscovery does not work and after manual entry of endpoints:
ID token validate failed with error: Only RS256 signature validation is supported. Token reports using EdDSAMaybe this is the reason -> https://github.com/BookStackApp/BookStack/issues/3206
-
@girish maybe the same problem with Freescout? https://freescout.net/module/saml/
Requirements
Signature Algorithm is RSA-SHA256. -
Yes we can support multiple ones https://github.com/panva/node-oidc-provider/blob/main/docs/README.md#jwks
I went for the recommended format first. Some more info about key algorithms https://www.scottbrady91.com/jose/jwts-which-signing-algorithm-should-i-use
-
Autodiscovery does not work and after manual entry of endpoints:
ID token validate failed with error: Only RS256 signature validation is supported. Token reports using EdDSAMaybe this is the reason -> https://github.com/BookStackApp/BookStack/issues/3206
@luckow I have added RS256 now, but so far I haven't managed to get to the point to see the signature validation error. Can you spot something missing in my test env file:
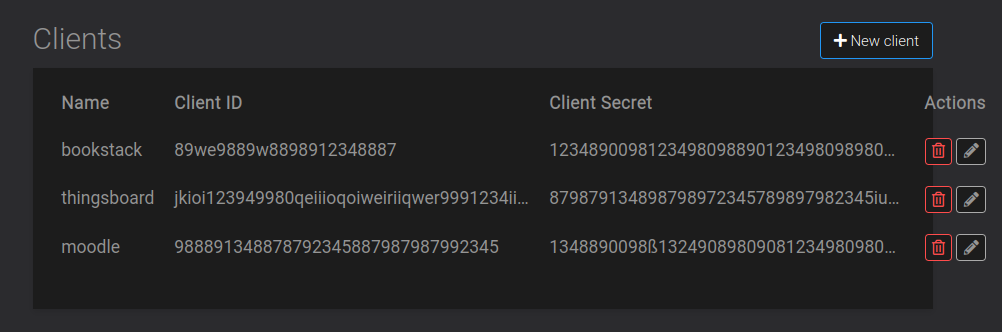
OIDC_NAME=Cloudron OIDC_DISPLAY_NAME_CLAIMS=name OIDC_CLIENT_ID=bookstackid OIDC_CLIENT_SECRET=bookstacksecret OIDC_ISSUER=https://nebulon.space OIDC_ISSUER_DISCOVER=false OIDC_AUTH_ENDPOINT=https://my.nebulon.space/openid/auth OIDC_TOKEN_ENDPOINT=https://my.nebulon.space/openid/tokenThe autodiscovery via .well-known also failed like you mentioned.
-
 N nebulon marked this topic as a question on
N nebulon marked this topic as a question on
-
@luckow I have added RS256 now, but so far I haven't managed to get to the point to see the signature validation error. Can you spot something missing in my test env file:
OIDC_NAME=Cloudron OIDC_DISPLAY_NAME_CLAIMS=name OIDC_CLIENT_ID=bookstackid OIDC_CLIENT_SECRET=bookstacksecret OIDC_ISSUER=https://nebulon.space OIDC_ISSUER_DISCOVER=false OIDC_AUTH_ENDPOINT=https://my.nebulon.space/openid/auth OIDC_TOKEN_ENDPOINT=https://my.nebulon.space/openid/tokenThe autodiscovery via .well-known also failed like you mentioned.
@nebulon I followed
https://www.bookstackapp.com/docs/admin/oidc-auth/With
OIDC_ISSUER_DISCOVER=truethe error isOIDC Discovery Error: Unexpected issuer value found on discovery responseWith
OIDC_ISSUER_DISCOVER=falsethe error isunrecognized route or not allowed method (GET on /interaction/uNAJ4bnbXdzrsVTA7pIl9/confirm)I have no idea, but maybe
OIDC_PUBLIC_KEY=https://my.example.org/openid/jwksis wrong.
The documentation says something with a .pem file:# Path to identity provider token signing public RSA key OIDC_PUBLIC_KEY=file:///keys/idp-public-key.pem -
@nebulon I followed
https://www.bookstackapp.com/docs/admin/oidc-auth/With
OIDC_ISSUER_DISCOVER=truethe error isOIDC Discovery Error: Unexpected issuer value found on discovery responseWith
OIDC_ISSUER_DISCOVER=falsethe error isunrecognized route or not allowed method (GET on /interaction/uNAJ4bnbXdzrsVTA7pIl9/confirm)I have no idea, but maybe
OIDC_PUBLIC_KEY=https://my.example.org/openid/jwksis wrong.
The documentation says something with a .pem file:# Path to identity provider token signing public RSA key OIDC_PUBLIC_KEY=file:///keys/idp-public-key.pem@luckow Update: after going "back" to the Bookstack home page (with the sso login button) and clicking again (with a valid login on my oic provider), I get the error again:
ID token validate failed with error: Only RS256 signature validation is supported. Token reports using EdDSA -
Wrong forum section, I will move this to support as it is more like a generic OpenID thread now.
I managed to get freescout working now with https://freescout.net/module/oauth-login/ and the added RS256 signature validation. We should be able to get this into 7.4.1
-
 N nebulon moved this topic from BookStack on
N nebulon moved this topic from BookStack on
-
Wrong forum section, I will move this to support as it is more like a generic OpenID thread now.
I managed to get freescout working now with https://freescout.net/module/oauth-login/ and the added RS256 signature validation. We should be able to get this into 7.4.1
-
 N nebulon marked this topic as a regular topic on
N nebulon marked this topic as a regular topic on
-
 G girish moved this topic from Support on
G girish moved this topic from Support on
-
To test Superset with Oauth we need an additional library
Apr 10 13:10:48 from authlib.integrations.flask_client import OAuth Apr 10 13:10:48 ModuleNotFoundError: No module named 'authlib'Referring to https://superset.apache.org/docs/installation/configuring-superset/#custom-oauth2-configuration
-
To test Superset with Oauth we need an additional library
Apr 10 13:10:48 from authlib.integrations.flask_client import OAuth Apr 10 13:10:48 ModuleNotFoundError: No module named 'authlib'Referring to https://superset.apache.org/docs/installation/configuring-superset/#custom-oauth2-configuration
-
 L luckow referenced this topic on
L luckow referenced this topic on
-
I'm still struggling to properly set up openID with my applications. For example with Leantime I get
The received provider https://my.domain.tld/openid does not match the local setting https://my.domain.tld/.well-known/openid-configurationafter authentification. And ctfreak will complain thatredirect_uris for native clients using http as a protocol can only use loopback addresses as hostnamesand using https won't work. -
 A andreasdueren referenced this topic on
A andreasdueren referenced this topic on
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login