nj
Posts
-
All Apps in Error state after updating to v8.0.6 -
All Apps in Error state after updating to v8.0.6All my cloudron apps (except those I installed manually) are now in Error state - stuck at Configuring.
Error shows they're failing because they cannot download icon from the app store.Previously, "Cloudron was updated from v8.0.4 to v8.0.6."
Need urgent fix
Also, the app store is not reachable with Error code
GET https://my.<domain>/api/v1/appstore/apps Status 424 { "status": "Failed Dependency", "message": "Internal error" }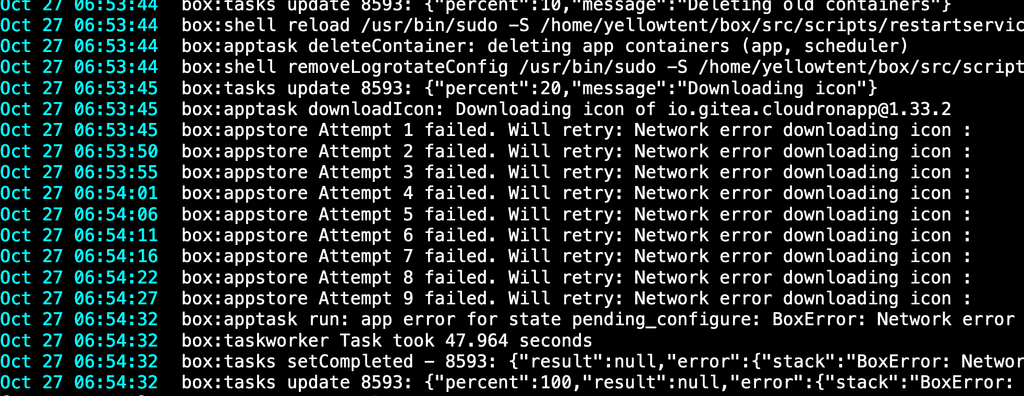
-
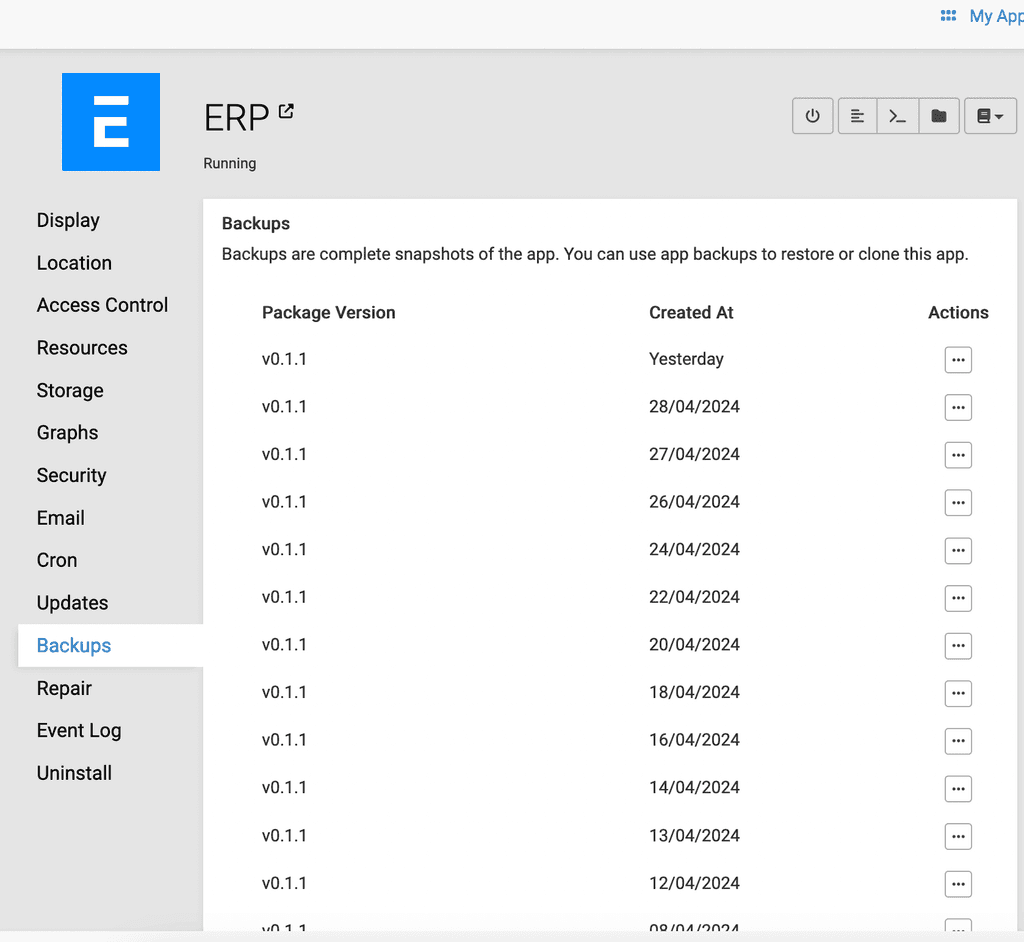
ERPNext - cost-effective ERP solutionCurrently, the data is automatically backed up. But I have also setup S3 backup to BackBlaze just to be double sure. Cloudron backup can be used for full restore of the site. It contains the database, files, and everything. ERPNext backup can be used to restore to a fresh installation.
Cloudron Auto Backup
S3 Backup Settings in ERPNext
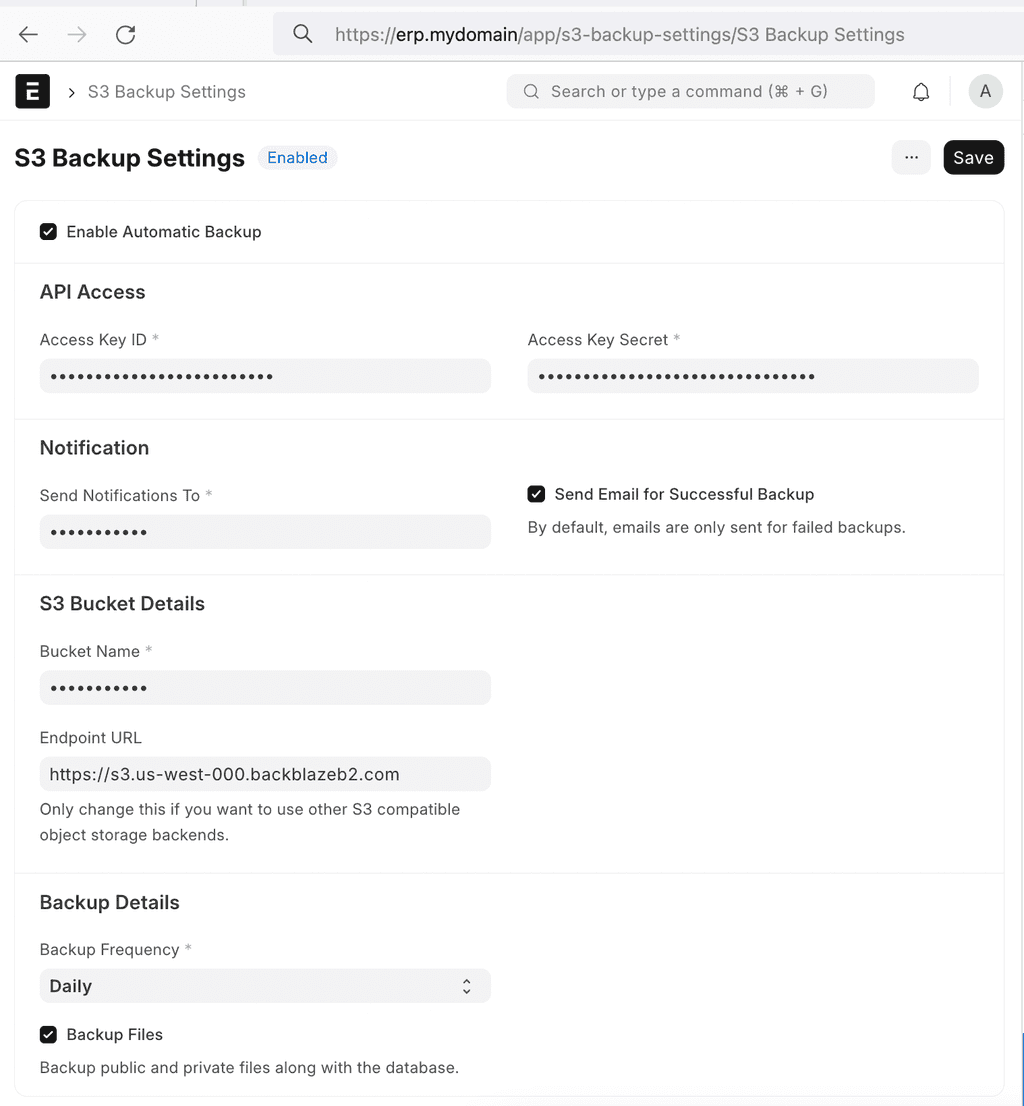
PS: I would highly recommend utilizing your cloud provider's "Automatic Backup" or "Automatic Snapshot" feature that allows you to automatically backup the whole VPS everyday. This way you have redundant backups. Make sure to use multiple vendors. For eg: if you host your VPS on AWS,
- Use AWS's automatic VPS backup system
- Configure Cloudron backups to say, DigitalOcean spaces
- Configure ERPNext backups to say, Backblaze
If all three are in a nearby region, latency won't be an issue, and you'd hardly ever deal with data loss, unless all three cloud providers close your account on the same day.
-
ERPNext - cost-effective ERP solutionYes, the package still works.
New Installation using my image
To directly install ERPNext if you haven't previously, use this command:
Remember to replace <yourdomain.com> with youre actual domain.cloudron login my.<yourdomain.com>
cloudron install --image njsubedi/cloudron-erpnext -l erp.<yourdomain.com>Open the file manager to look for the credentials.
If you need to login with LDAP, you can do that by using the terminal of this app, and run
/app/pkg/setup-ldap.sh addOtherwise, that's all you need to do.
Updating
If you previously used ths app and want to continue using version-14, you need to do is run
gosu cloudron bench update --resetonce in a while to keep things up to date.Now, I have upgraded the code to use version-15 by default.
If you were previously running on version-14 and now need to update to version-15 that's pretty easy too.
Just run
gosu cloudron bench switch-to-branch version-15 frappe erpnext --upgradeThen run
gosu cloudron bench migrate -
Logchimp: Build better products with customer feedbackTrack, manage, engage, and analyse your customer' feedback to make product decisions with ease.
https://logchimp.codecarrot.net/
https://github.com/logchimp/logchimp/
-
Directus fail to create an user from Cloudron Open IDI also have this problem. The error is that I can't use Login with cloudron because their default authentication source (provider) is set to 'default'. I can change that to 'cloudron'. But still while logging in, it will say 'invalid_provider'. Once I locked my admin account out by changing the source to 'cloudron' then changed the provider using postgres query. Issue still remains unsolved, but since all users have their passwords it's not been an urgent problem. But still.. worth looking into it.
-
No Update for around 6 monthsAfter this I simply retried update and it worked. And now all apps are updating as well. Thank you.
-
No Update for around 6 months~# apt install linux-modules-5.15.0-72-generic linux-headers-5.15.0-72-generic Reading package lists... Done Building dependency tree... Done Reading state information... Done linux-headers-5.15.0-72-generic is already the newest version (5.15.0-72.79). linux-headers-5.15.0-72-generic set to manually installed. linux-modules-5.15.0-72-generic is already the newest version (5.15.0-72.79). linux-modules-5.15.0-72-generic set to manually installed. The following packages were automatically installed and are no longer required: accountsservice alsa-topology-conf alsa-ucm-conf at bsdmainutils cryptsetup-run dconf-gsettings-backend dconf-service g++-9 glib-networking glib-networking-common glib-networking-services gsettings-desktop-schemas language-selector-common libaccountsservice0 libasn1-8-heimdal libasound2 libasound2-data libcanberra0 libcbor0.6 libdconf1 libdns-export1109 libffi7 libfl2 libfstrm0 libfuse2 libfwupdplugin1 libgdk-pixbuf-xlib-2.0-0 libgdk-pixbuf2.0-0 libgssapi3-heimdal libhcrypto4-heimdal libheimbase1-heimdal libheimntlm0-heimdal libhogweed5 libhx509-5-heimdal libicu66 libisl22 libjson-c4 libkrb5-26-heimdal libldap-2.4-2 libmpdec2 libnettle7 libntfs-3g883 libogg0 libperl5.30 libproxy1v5 libpython3.8 libpython3.8-minimal libpython3.8-stdlib libreadline5 libroken18-heimdal libsoup2.4-1 libsoup2.4-common libssl1.1 libstdc++-9-dev libtdb1 liburcu6 libvorbis0a libvorbisfile3 libwebp6 libwind0-heimdal libxmlb1 ltrace lz4 ncal perl-modules-5.30 popularity-contest python3-entrypoints python3-requests-unixsocket python3-simplejson python3.8 python3.8-minimal session-migration sound-theme-freedesktop Use 'apt autoremove' to remove them. 0 upgraded, 0 newly installed, 0 to remove and 125 not upgraded. -
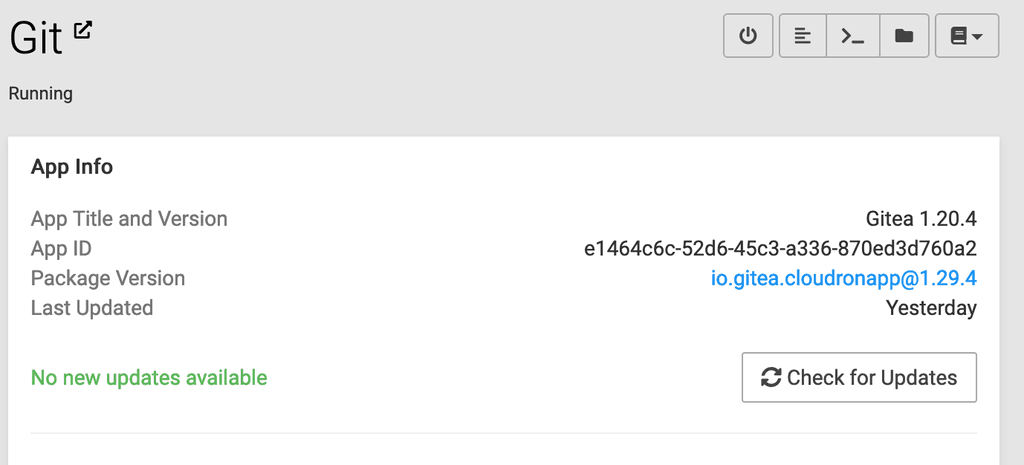
No Update for around 6 monthsMaybe this is the cause? Platform version: v7.4.3 (Ubuntu 22.04.1 LTS) Where can I find more details about this error? I had always thought the system auto-updates on a scheduled time.

Screenshot showing no update available for Gitea.
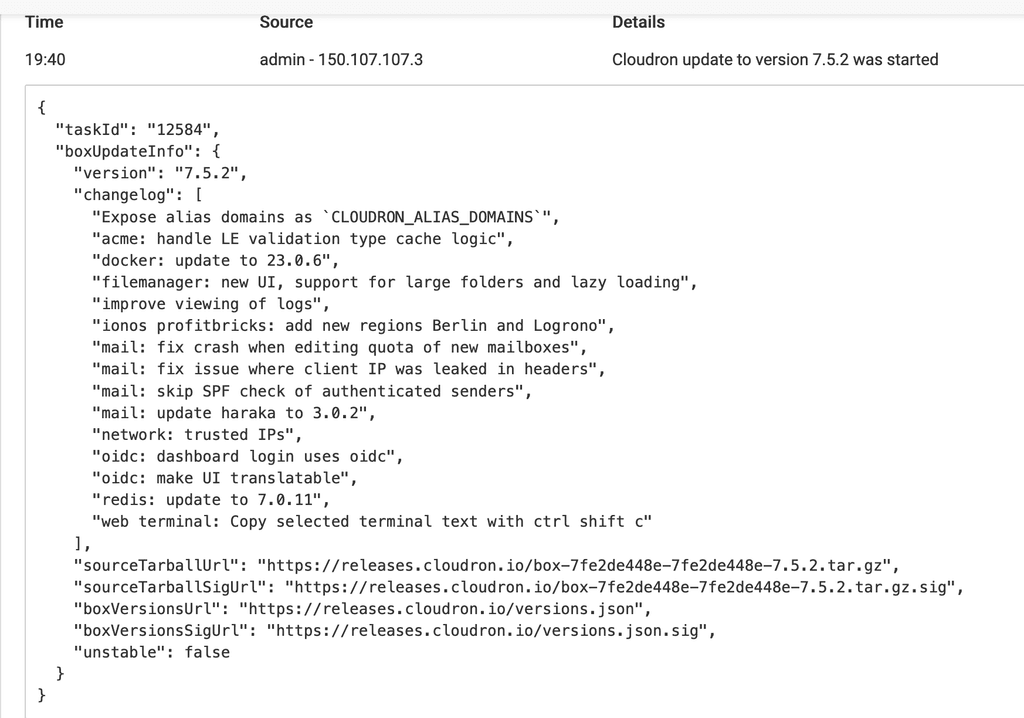
Screenshot showing Cloudron platform update starting.
Screenshot showing update failure.
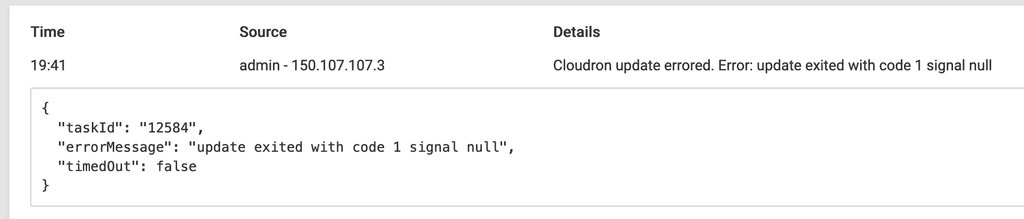
Logs
# tail -n 100 -f /home/yellowtent/platformdata/logs/tasks/12583.log 2024-03-02T13:53:36.131Z box:settings initCache: pre-load settings 2024-03-02T13:53:36.143Z box:taskworker Starting task 12583. Logs are at /home/yellowtent/platformdata/logs/tasks/12583.log 2024-03-02T13:53:36.145Z box:tasks update 12583: {"percent":1,"message":"Checking disk space"} 2024-03-02T13:53:36.155Z box:tasks update 12583: {"percent":5,"message":"Downloading and verifying release"} 2024-03-02T13:53:36.156Z box:updater Downloading https://releases.cloudron.io/versions.json to /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:36.156Z box:updater downloadUrl: curl -s --fail https://releases.cloudron.io/versions.json -o /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:36.157Z box:shell downloadUrl spawn: /usr/bin/curl -s --fail https://releases.cloudron.io/versions.json -o /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:38.171Z box:updater downloadUrl: downloaded https://releases.cloudron.io/versions.json to /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:38.171Z box:updater Downloading https://releases.cloudron.io/versions.json.sig to /home/yellowtent/platformdata/update/versions.json.sig 2024-03-02T13:53:38.171Z box:updater downloadUrl: curl -s --fail https://releases.cloudron.io/versions.json.sig -o /home/yellowtent/platformdata/update/versions.json.sig 2024-03-02T13:53:38.171Z box:shell downloadUrl spawn: /usr/bin/curl -s --fail https://releases.cloudron.io/versions.json.sig -o /home/yellowtent/platformdata/update/versions.json.sig 2024-03-02T13:53:39.127Z box:updater downloadUrl: downloaded https://releases.cloudron.io/versions.json.sig to /home/yellowtent/platformdata/update/versions.json.sig 2024-03-02T13:53:39.127Z box:updater gpgVerify: /usr/bin/gpg --status-fd 1 --no-default-keyring --keyring /home/yellowtent/box/src/releases.gpg --verify /home/yellowtent/platformdata/update/versions.json.sig /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:39.127Z box:shell gpgVerify exec: /usr/bin/gpg --status-fd 1 --no-default-keyring --keyring /home/yellowtent/box/src/releases.gpg --verify /home/yellowtent/platformdata/update/versions.json.sig /home/yellowtent/platformdata/update/versions.json 2024-03-02T13:53:39.139Z box:shell gpgVerify (stdout): [GNUPG:] NEWSIG [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] SIG_ID 1nIHhoIVnhz3dcSh7GrpK492EEc 2024-01-23 1706050072 [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] GOODSIG 0A372F8703C493CC Cloudron UG <admin@cloudron.io> [GNUPG:] VALIDSIG 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 2024-01-23 1706050072 0 4 0 1 10 00 0EADB19CDDA23CD0FE71E3470A372F8703C493CC [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] TRUST_UNDEFINED 0 pgp [GNUPG:] VERIFICATION_COMPLIANCE_MODE 23 2024-03-02T13:53:39.139Z box:shell gpgVerify (stderr): gpg: Signature made Tue Jan 23 22:47:52 2024 UTC gpg: using RSA key 0EADB19CDDA23CD0FE71E3470A372F8703C493CC gpg: Good signature from "Cloudron UG <admin@cloudron.io>" [unknown] gpg: WARNING: This key is not certified with a trusted signature! gpg: There is no indication that the signature belongs to the owner. Primary key fingerprint: 0EAD B19C DDA2 3CD0 FE71 E347 0A37 2F87 03C4 93CC 2024-03-02T13:53:39.141Z box:updater Downloading https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz to /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:39.141Z box:updater downloadUrl: curl -s --fail https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz -o /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:39.141Z box:shell downloadUrl spawn: /usr/bin/curl -s --fail https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz -o /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:44.222Z box:updater downloadUrl: downloaded https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz to /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:44.223Z box:updater Downloading https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz.sig to /home/yellowtent/platformdata/update/box.tar.gz.sig 2024-03-02T13:53:44.223Z box:updater downloadUrl: curl -s --fail https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz.sig -o /home/yellowtent/platformdata/update/box.tar.gz.sig 2024-03-02T13:53:44.223Z box:shell downloadUrl spawn: /usr/bin/curl -s --fail https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz.sig -o /home/yellowtent/platformdata/update/box.tar.gz.sig 2024-03-02T13:53:45.134Z box:updater downloadUrl: downloaded https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz.sig to /home/yellowtent/platformdata/update/box.tar.gz.sig 2024-03-02T13:53:45.134Z box:updater gpgVerify: /usr/bin/gpg --status-fd 1 --no-default-keyring --keyring /home/yellowtent/box/src/releases.gpg --verify /home/yellowtent/platformdata/update/box.tar.gz.sig /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:45.134Z box:shell gpgVerify exec: /usr/bin/gpg --status-fd 1 --no-default-keyring --keyring /home/yellowtent/box/src/releases.gpg --verify /home/yellowtent/platformdata/update/box.tar.gz.sig /home/yellowtent/platformdata/update/box.tar.gz 2024-03-02T13:53:45.284Z box:shell gpgVerify (stdout): [GNUPG:] NEWSIG [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] SIG_ID vwqItj31YcBTqdpnuE5ghvxnZKM 2023-08-29 1693311609 [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] GOODSIG 0A372F8703C493CC Cloudron UG <admin@cloudron.io> [GNUPG:] VALIDSIG 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 2023-08-29 1693311609 0 4 0 1 10 00 0EADB19CDDA23CD0FE71E3470A372F8703C493CC [GNUPG:] KEY_CONSIDERED 0EADB19CDDA23CD0FE71E3470A372F8703C493CC 0 [GNUPG:] TRUST_UNDEFINED 0 pgp [GNUPG:] VERIFICATION_COMPLIANCE_MODE 23 2024-03-02T13:53:45.284Z box:shell gpgVerify (stderr): gpg: Signature made Tue Aug 29 12:20:09 2023 UTC gpg: using RSA key 0EADB19CDDA23CD0FE71E3470A372F8703C493CC gpg: Good signature from "Cloudron UG <admin@cloudron.io>" [unknown] gpg: WARNING: This key is not certified with a trusted signature! gpg: There is no indication that the signature belongs to the owner. Primary key fingerprint: 0EAD B19C DDA2 3CD0 FE71 E347 0A37 2F87 03C4 93CC 2024-03-02T13:53:45.284Z box:updater extractTarball: tar -zxf /home/yellowtent/platformdata/update/box.tar.gz -C /tmp/box-2567641860 2024-03-02T13:53:45.284Z box:shell extractTarball spawn: /bin/tar -zxf /home/yellowtent/platformdata/update/box.tar.gz -C /tmp/box-2567641860 2024-03-02T13:53:46.490Z box:updater extractTarball: extracted /home/yellowtent/platformdata/update/box.tar.gz to /tmp/box-2567641860 2024-03-02T13:53:46.490Z box:updater Updating box with https://releases.cloudron.io/box-7fe2de448e-7fe2de448e-7.5.2.tar.gz 2024-03-02T13:53:46.490Z box:tasks update 12583: {"percent":70,"message":"Installing update"} 2024-03-02T13:53:46.491Z box:shell update spawn: /usr/bin/sudo -S /home/yellowtent/box/src/scripts/update.sh /tmp/box-2567641860 2024-03-02T13:53:46.506Z box:shell update (stdout): Updating Cloudron with /tmp/box-2567641860 2024-03-02T13:53:46.506Z box:shell update (stdout): => reset service cloudron-updater status (of previous update) 2024-03-02T13:53:46.509Z box:shell update (stdout): => Run installer.sh as cloudron-updater. 2024-03-02T13:53:46.511Z box:shell update (stdout): => starting service cloudron-updater. see logs at /home/yellowtent/platformdata/logs/updater/cloudron-updater-2024-03-02_13-53-46.log 2024-03-02T13:53:46.541Z box:shell update (stderr): Running as unit: cloudron-updater.service 2024-03-02T13:53:46.544Z box:shell update (stdout): cloudron-updater is still active. will check in 5 seconds 2024-03-02T13:53:51.549Z box:shell update (stdout): cloudron-updater is still active. will check in 5 seconds 2024-03-02T13:53:56.554Z box:shell update (stdout): cloudron-updater is still active. will check in 5 seconds 2024-03-02T13:54:01.559Z box:shell update (stdout): cloudron-updater is still active. will check in 5 seconds 2024-03-02T13:54:06.565Z box:shell update (stdout): => cloudron-updater has failed 2024-03-02T13:54:06.566Z box:shell update code: 1, signal: null 2024-03-02T13:54:06.567Z box:taskworker Task took 30.475 seconds 2024-03-02T13:54:06.567Z box:tasks setCompleted - 12583: {"result":null,"error":{"stack":"BoxError: update exited with code 1 signal null\n at ChildProcess.<anonymous> (/home/yellowtent/box/src/shell.js:78:17)\n at ChildProcess.emit (node:events:513:28)\n at Process.ChildProcess._handle.onexit (node:internal/child_process:293:12)","name":"BoxError","reason":"Spawn Error","details":{},"message":"update exited with code 1 signal null","code":1,"signal":null}} 2024-03-02T13:54:06.567Z box:tasks update 12583: {"percent":100,"result":null,"error":{"stack":"BoxError: update exited with code 1 signal null\n at ChildProcess.<anonymous> (/home/yellowtent/box/src/shell.js:78:17)\n at ChildProcess.emit (node:events:513:28)\n at Process.ChildProcess._handle.onexit (node:internal/child_process:293:12)","name":"BoxError","reason":"Spawn Error","details":{},"message":"update exited with code 1 signal null","code":1,"signal":null}} BoxError: update exited with code 1 signal null at ChildProcess.<anonymous> (/home/yellowtent/box/src/shell.js:78:17) at ChildProcess.emit (node:events:513:28) at Process.ChildProcess._handle.onexit (node:internal/child_process:293:12)Outcome of
dpkg --configure -a:~# dpkg --configure -a dpkg: dependency problems prevent configuration of linux-image-generic: linux-image-generic depends on linux-modules-extra-5.15.0-72-generic; however: Package linux-modules-extra-5.15.0-72-generic is not installed. dpkg: error processing package linux-image-generic (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-generic: linux-generic depends on linux-image-generic (= 5.15.0.72.70); however: Package linux-image-generic is not configured yet. dpkg: error processing package linux-generic (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-image-5.15.0-72-generic: linux-image-5.15.0-72-generic depends on linux-modules-5.15.0-72-generic; however: Package linux-modules-5.15.0-72-generic is not installed. dpkg: error processing package linux-image-5.15.0-72-generic (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-image-virtual: linux-image-virtual depends on linux-image-5.15.0-72-generic; however: Package linux-image-5.15.0-72-generic is not configured yet. dpkg: error processing package linux-image-virtual (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-headers-5.15.0-72-generic: linux-headers-5.15.0-72-generic depends on linux-headers-5.15.0-72; however: Package linux-headers-5.15.0-72 is not installed. dpkg: error processing package linux-headers-5.15.0-72-generic (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-headers-generic: linux-headers-generic depends on linux-headers-5.15.0-72-generic; however: Package linux-headers-5.15.0-72-generic is not configured yet. dpkg: error processing package linux-headers-generic (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-virtual: linux-virtual depends on linux-image-virtual (= 5.15.0.72.70); however: Package linux-image-virtual is not configured yet. dpkg: error processing package linux-virtual (--configure): dependency problems - leaving unconfigured dpkg: dependency problems prevent configuration of linux-headers-virtual: linux-headers-virtual depends on linux-headers-generic (= 5.15.0.72.70); however: Package linux-headers-generic is not configured yet. dpkg: error processing package linux-headers-virtual (--configure): dependency problems - leaving unconfigured Errors were encountered while processing: linux-image-generic linux-generic linux-image-5.15.0-72-generic linux-image-virtual linux-headers-5.15.0-72-generic linux-headers-generic linux-virtual linux-headers-virtual -
No Update for around 6 months -
OpenID Connect Server not working in Outline NotesI'm sorry, it was an error on my part. I had used the URL
/openid/userinfoinstead of/openid/me. -
OpenID Connect Server not working in Outline NotesI understood that profile doesn’t include “email” and email is a separate scope. But still with stock setup in Keycloak vs Cloudron, the Keycloak version works and Cloudron version of the provider doesn’t work. This is what’s strange.
-
OpenID Connect Server not working in Outline Notes@nebulon said in OpenID Connect Server not working in Outline Notes:
It may be that your Keycloak client settings automatically add email claims by default, for the standard OpenID those have to be specified when the client flow is initiated https://docs.cloudron.io/user-management/#scopes-and-claims
But it's the Outline app that initiates auth request with the Cloudron OpenID Connect server. I tried both
preferred_usernameas well assubbut none worked. All other settings match with Cloudron's recommendations.Is it because
profiledoesn't includeemail? -
OpenID Connect Server not working in Outline NotesThe app gets stuck in a loop: auth -> tocloudron -> auth page. The following error is thrown by Outline:
Highlight: "UnauthorizedError: An email field was not returned in the profile parameter, but is required."
I think the provider isn't sending back the user's email? Please check. Simply replacing the url of my.cloudron.tld to that of keycloak works, so there's something missing bit in the Cloudron implementation. Thanks!
{"error":"An email field was not returned in the profile parameter, but is required.","stack":"UnauthorizedError: An email field was not returned in the profile parameter, but is required.\n at AuthenticationError (/app/code/build/server/errors.js:38:34)\n at OAuth2Strategy._verify (/app/code/build/server/routes/auth/providers/oidc.js:60:47)\n at /app/code/node_modules/passport-oauth2/lib/strategy.js:196:24\n at OAuth2Strategy._passportOauth.Strategy.userProfile (/app/code/build/server/routes/auth/providers/oidc.js:32:12)\n at processTicksAndRejections (node:internal/process/task_queues:96:5)","level":"error","message":"Error during authentication"} -
Custom Cache-control headers@staff
Tagging for visibility of the post. -
Custom Cache-control headersThe header currently sent by Surfer for all requests is
Cache-Control: public, max-age=0This setting causes the browsers to re-request everything that could have been cached instead. If the
max-agevalue could be customizable from settings or somehow else, that would be a lot less strain on the Surfer on Cloudron.My use-case:
I run Surfer behind Cloudflare, and Cloudflare honors the cache settings, but only ifmax-ageis set to a non-zero value. Basically Cloudflare is not caching anything and my Surfer instance is constantly running out of memory because of the number of requests. -
MariaDB Addon@girish I have figured out a solution that doesn’t require admin permissions to ERPNext. It’s just that they use MariaDB specific commands here and there. That’s why MySQL addon is not useful at all.
Multiple databases works kinda fine but needs patching the source because ERPNext likes to use the same value for db-user and db-name; in fact there’s no way to give it the db-user. The name of the database is itself is considered username.
While building this addon, I would recommend setting the user’s name and database the same - ie. without prepending the same string with ‘db’ or ‘user’
Multiple databases isn’t required as ERPNext doesn’t work really well as a multi-site ERP anyway.
-
MariaDB AddonSome apps like ERPNext are only optimized for MariaDB and use MariaDB specific features. Slowly MariaDB is getting incompatible with MySQL by adding features like custom sequences not available in MySQL.
From a Cloudron dev’s POV, adding MariaDB as an addon is a trivial task because MySQL is already there. Please add MariaDB as an addon. Thank you!
-
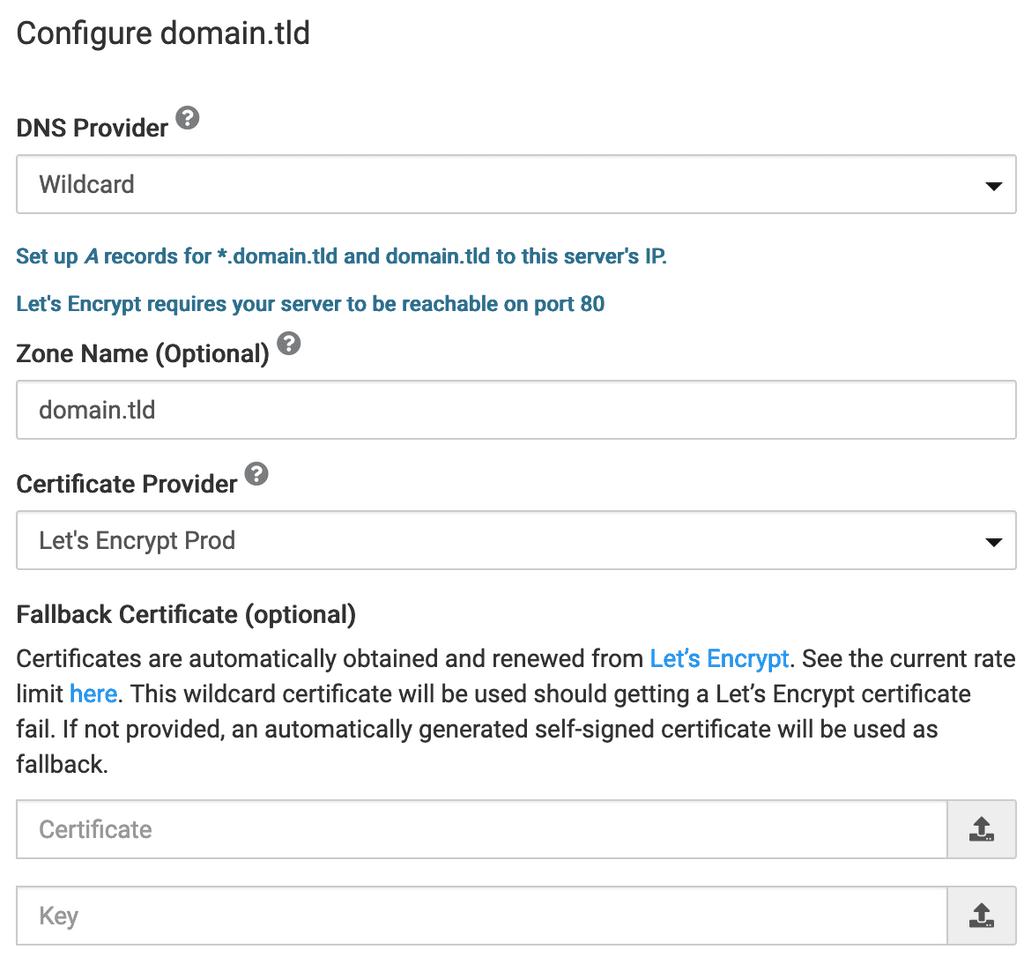
Let's Encrypt Didn't seem to auto-renewI can confirm the issue. Certificate of other domains added to Cloudron aren't renewed. Primary domain seems to be renewed.
Some certs are due 4 days.
 Good thing I had alerts enabled so I got notified.
Good thing I had alerts enabled so I got notified.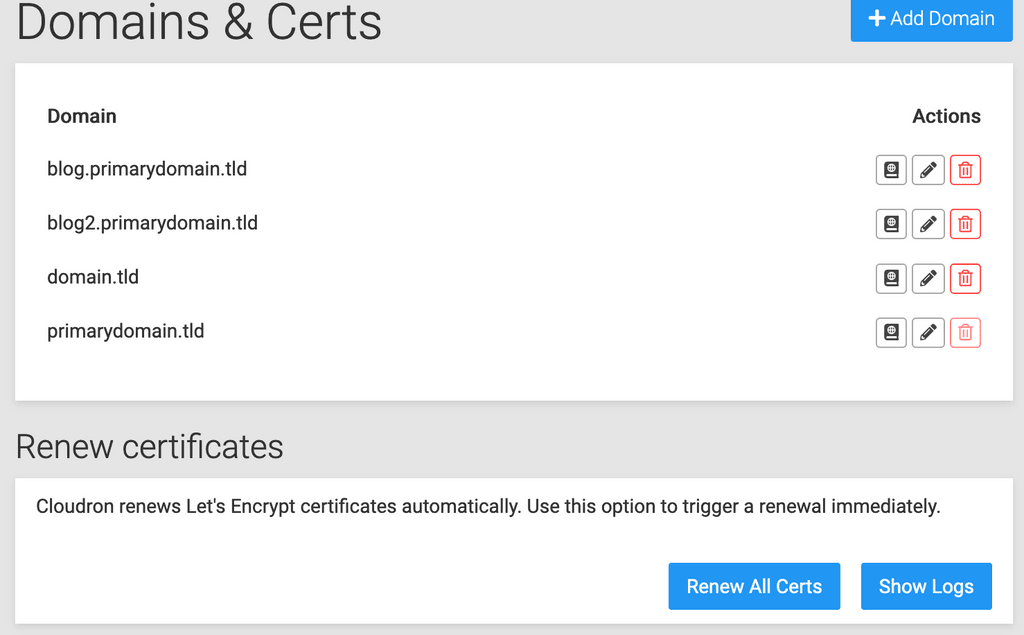
Domain provider is Wildcard. Both domain.tld and *.domain.tld point to the cloudron (since last 1-2 years).
Renew all Certs shows "Configuring apps .. or something" and the progressbar disappears.
- "Show Logs" shows empty window.
- Download full logs -> 1 byte empty file
-
ERPNext - cost-effective ERP solutionI spent several days to make ErpNext work with Cloudron MySQL or Postgres. Unfortunately, postgres support is still a work in progress in ErpNext upstream and the project uses some features like
CREATE SEQUENCEthat are only available in MySQL, not in MariaDB. That's why the current version of this package is the most stable one.My suggestion to @staff if you can, please add the MariaDB addon alongside the MySQL addon. It should be extremely easy to add because of the similarity with MySQL. There are so many open source software that use MariaDB, and will sooner or later be incompatible with MySQL.